Prepared by:
HALBORN
Last Updated 05/21/2024
Date of Engagement: April 22nd, 2024 - May 13th, 2024
Summary
100% of all REPORTED Findings have been addressed
All findings
8
Critical
0
High
0
Medium
0
Low
4
Informational
4
Table of Contents
- 1. Introduction
- 2. Assessment summary
- 3. Test approach and methodology
- 4. Risk methodology
- 5. Scope
- 6. Assessment summary & findings overview
- 7. Findings & Tech Details
- 7.1 Centralization risk in ifov2.finalwithdraw() function
- 7.2 Erc20 permits are vulnerable to griefing via frontrunning
- 7.3 Direct usage of ecrecover allows signature malleability
- 7.4 Missing disableinitializers() call
- 7.5 Floating pragma
- 7.6 Unoptimized loops
- 7.7 Lack of a double-step transferownership() pattern
- 7.8 Unneeded initialization of uint256 variables to 0
- 8. Automated Testing
1. Introduction
Secta Finance engaged Halborn to conduct a security assessment on their smart contracts beginning on April 22nd, 2024 and ending on May 10th, 2024. The security assessment was scoped to the smart contracts provided in the following GitHub repositories:
2. Assessment Summary
The team at Halborn was provided three weeks for the engagement and assigned a full-time security engineer to verify the security of the smart contracts. The security engineer is a blockchain and smart-contract security expert with advanced penetration testing, smart-contract hacking, and deep knowledge of multiple blockchain protocols.
The purpose of this assessment is to:
- Ensure that smart contract functions operate as intended.
- Identify potential security issues with the smart contracts.
In summary, Halborn identified some security risks that were mostly addressed by the Secta Finance team.
3. Test Approach and Methodology
Halborn performed a combination of manual and automated security testing to balance efficiency, timeliness, practicality, and accuracy in regard to the scope of this assessment. While manual testing is recommended to uncover flaws in logic, process, and implementation; automated testing techniques help enhance coverage of the code and can quickly identify items that do not follow the security best practices. The following phases and associated tools were used during the assessment:
- Research into architecture and purpose.
- Smart contract manual code review and walkthrough.
- Graphing out functionality and contract logic/connectivity/functions. (`solgraph`)
- Manual assessment of use and safety for the critical Solidity variables and functions in scope to identify any arithmetic related vulnerability classes.
- Manual testing by custom scripts.
- Static Analysis of security for scoped contract, and imported functions. (`Slither`)
- Testnet deployment. (`Foundry`)
4. RISK METHODOLOGY
4.1 EXPLOITABILITY
Attack Origin (AO):
Attack Cost (AC):
Attack Complexity (AX):
Metrics:
| EXPLOITABILITY METRIC () | METRIC VALUE | NUMERICAL VALUE |
|---|---|---|
| Attack Origin (AO) | Arbitrary (AO:A) Specific (AO:S) | 1 0.2 |
| Attack Cost (AC) | Low (AC:L) Medium (AC:M) High (AC:H) | 1 0.67 0.33 |
| Attack Complexity (AX) | Low (AX:L) Medium (AX:M) High (AX:H) | 1 0.67 0.33 |
4.2 IMPACT
Confidentiality (C):
Integrity (I):
Availability (A):
Deposit (D):
Yield (Y):
Metrics:
| IMPACT METRIC () | METRIC VALUE | NUMERICAL VALUE |
|---|---|---|
| Confidentiality (C) | None (I:N) Low (I:L) Medium (I:M) High (I:H) Critical (I:C) | 0 0.25 0.5 0.75 1 |
| Integrity (I) | None (I:N) Low (I:L) Medium (I:M) High (I:H) Critical (I:C) | 0 0.25 0.5 0.75 1 |
| Availability (A) | None (A:N) Low (A:L) Medium (A:M) High (A:H) Critical (A:C) | 0 0.25 0.5 0.75 1 |
| Deposit (D) | None (D:N) Low (D:L) Medium (D:M) High (D:H) Critical (D:C) | 0 0.25 0.5 0.75 1 |
| Yield (Y) | None (Y:N) Low (Y:L) Medium (Y:M) High (Y:H) Critical (Y:C) | 0 0.25 0.5 0.75 1 |
4.3 SEVERITY COEFFICIENT
Reversibility (R):
Scope (S):
Metrics:
| SEVERITY COEFFICIENT () | COEFFICIENT VALUE | NUMERICAL VALUE |
|---|---|---|
| Reversibility () | None (R:N) Partial (R:P) Full (R:F) | 1 0.5 0.25 |
| Scope () | Changed (S:C) Unchanged (S:U) | 1.25 1 |
| Severity | Score Value Range |
|---|---|
| Critical | 9 - 10 |
| High | 7 - 8.9 |
| Medium | 4.5 - 6.9 |
| Low | 2 - 4.4 |
| Informational | 0 - 1.9 |
5. SCOPE
- exchange-protocol/contracts/SectaERC20.sol
- exchange-protocol/contracts/SectaFactory.sol
- exchange-protocol/contracts/SectaPair.sol
- router/contracts/SmartRouter.sol
- router/contracts/V2SwapRouter.sol
- router/contracts/V3SwapRouter.sol
6. Assessment Summary & Findings Overview
Critical
0
High
0
Medium
0
Low
4
Informational
4
| Security analysis | Risk level | Remediation Date |
|---|---|---|
| Centralization risk in IFOV2.finalWithdraw() function | Low | Solved - 05/16/2024 |
| ERC20 permits are vulnerable to griefing via frontrunning | Low | Risk Accepted |
| Direct usage of ecrecover allows signature malleability | Low | Risk Accepted |
| Missing disableInitializers() call | Low | Risk Accepted |
| Floating pragma | Informational | Acknowledged |
| Unoptimized loops | Informational | Acknowledged |
| Lack of a double-step transferOwnership() pattern | Informational | Acknowledged |
| Unneeded initialization of uint256 variables to 0 | Informational | Acknowledged |
7. Findings & Tech Details
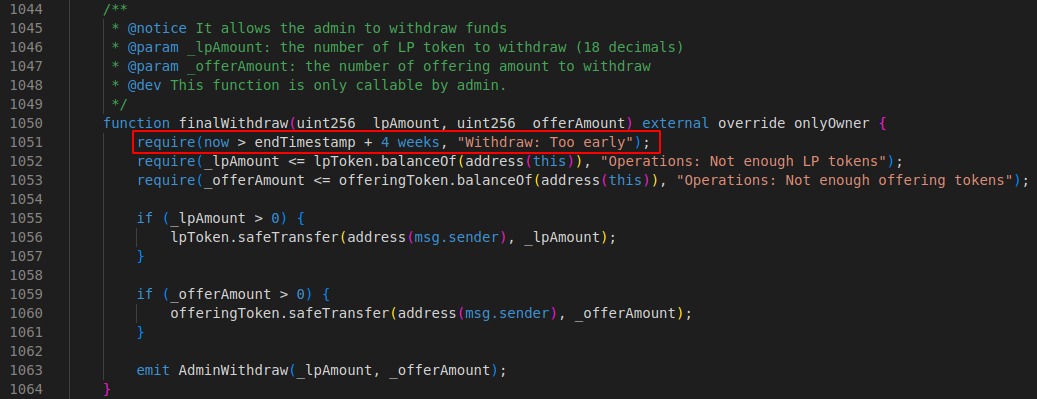
7.1 Centralization risk in IFOV2.finalWithdraw() function
//
Description
The contract IFOV2 implements the function finalWithdraw():

This function allows the admins to withdraw the funds from the contract. However, there is no time restriction and admins can withdraw these funds at any time. Consequently, a malicious admin could withdraw all the funds including the users' LP tokens deposited in the contract right before the endTimestamp is reached, and before the users have harvested.
BVSS
Recommendation
It is recommended to update the finalWithdraw() function, so admins can only withdraw the funds after a cooldown period has passed. This period should allow users enough time to harvest the pools. For example:
Remediation Plan
SOLVED : The Secta Finance team solved the issue by implementing the recommended solution.
Remediation Hash
7.2 ERC20 permits are vulnerable to griefing via frontrunning
//
Description
The usages of the permit ERC20 extension in the code can be frontrun by any party that witnesses transactions prior to block inclusion. This is a griefing vector that will cause user transactions to fail if the associated permit has already been consumed. See this article for more details. While the risk of this seems quite low (very little incentive to perform the attack, and if the centralized sequencer is trustworthy, it will not grief users or reveal their transaction inappropriately), it could cause a bad experience for users.
BVSS
Recommendation
Consider implementing an allowance check as a fallback if permit validation fails, so that transactions for which the permit was already consumed do no revert.
Remediation Plan
RISK ACCEPTED: The Secta Finance team accepted this risk of this finding.
References
7.3 Direct usage of ecrecover allows signature malleability
//
Description
Multiple functions across the protocol codebase make use of the Ethereum-specfic ecrecover function directly to verify the given signatures. However, using ecrecover directly allows malleable (non-unique) signatures and thus is susceptible to replay attacks. Although replay attacks are not possible as the contracts correctly use different mitigations (domain separator, nonces...), ensuring the signatures are not malleable is considered a best practice (and so is checking that the_signeris different than the address(0), where address(0) means an invalid signature).
BVSS
Recommendation
It is recommended to use the recover function from OpenZeppelin's ECDSA library for signature verification.
Remediation Plan
RISK ACCEPTED: The Secta Finance team accepted this risk of this finding.
References
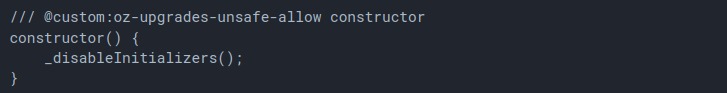
7.4 Missing disableInitializers() call
//
Description
Multiple contracts are using the Initializable module from OpenZeppelin. In order to prevent leaving the contracts uninitialized OpenZeppelin's documentation recommends adding the _disableInitializers function in the constructor to automatically lock the contracts when they are deployed:
BVSS
Recommendation
Consider calling the _disableInitializers function in all the contracts' constructor.
Remediation Plan
RISK ACCEPTED: The Secta Finance team accepted this risk of this finding.
References
7.5 Floating pragma
//
Description
Contracts should be deployed with the same compiler version and flags used during development and testing. Locking the pragma helps to ensure that contracts do not accidentally get deployed using another pragma. For example, an outdated pragma version might introduce bugs that affect the contract system negatively.
BVSS
Recommendation
Consider locking the pragma version in the smart contracts. It is not recommended to use a floating pragma in production.
For example: pragma solidity 0.6.12;
Remediation Plan
ACKNOWLEDGED: The Secta Finance team acknowledged this finding.
References
7.6 Unoptimized loops
//
Description
If a loop is iterated many times, the amount of gas required to execute the function increases significantly. In Solidity, excessive looping can cause a function to use more than the maximum allowed gas, which causes the function to fail.
BVSS
Recommendation
To reduce gas consumption, it is recommended to find ways to optimize the loop or potentially break the loop into smaller batches. The following pattern can also be used:
uint256 cachedLen = array.length;
for(uint i; i < cachedLen;){
unchecked {
++i;
}
}Remediation Plan
ACKNOWLEDGED: The Secta Finance team acknowledged this finding.
References
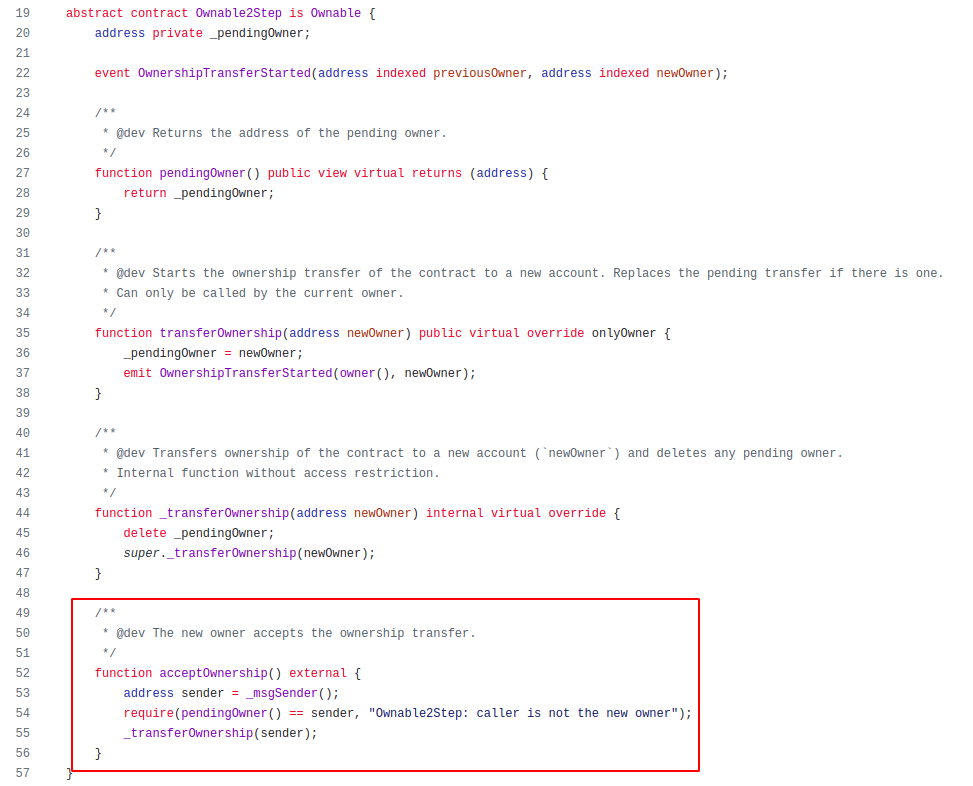
7.7 Lack of a double-step transferOwnership() pattern
//
Description
The current ownership transfer process for all the contracts inheriting from Ownable or OwnableUpgradeable involves the current owner calling the transferOwnership() function:
function transferOwnership(address newOwner) public virtual onlyOwner {
require(newOwner != address(0), "Ownable: new owner is the zero address");
_setOwner(newOwner);
}If the nominated EOA account is not a valid account, it is entirely possible that the owner may accidentally transfer ownership to an uncontrolled account, losing the access to all functions with the onlyOwner modifier.
BVSS
Recommendation
It is recommended to implement a two-step process where the owner nominates an account and the nominated account needs to call an acceptOwnership() function for the transfer of the ownership to fully succeed. This ensures the nominated EOA account is a valid and active account. This can be easily achieved by using OpenZeppelin's Ownable2Step contract instead of Ownable:
Remediation Plan
ACKNOWLEDGED: The Secta Finance team acknowledged this finding.
7.8 Unneeded initialization of uint256 variables to 0
//
Description
In the IFOV2 contract some variables are reinitialized to 0:
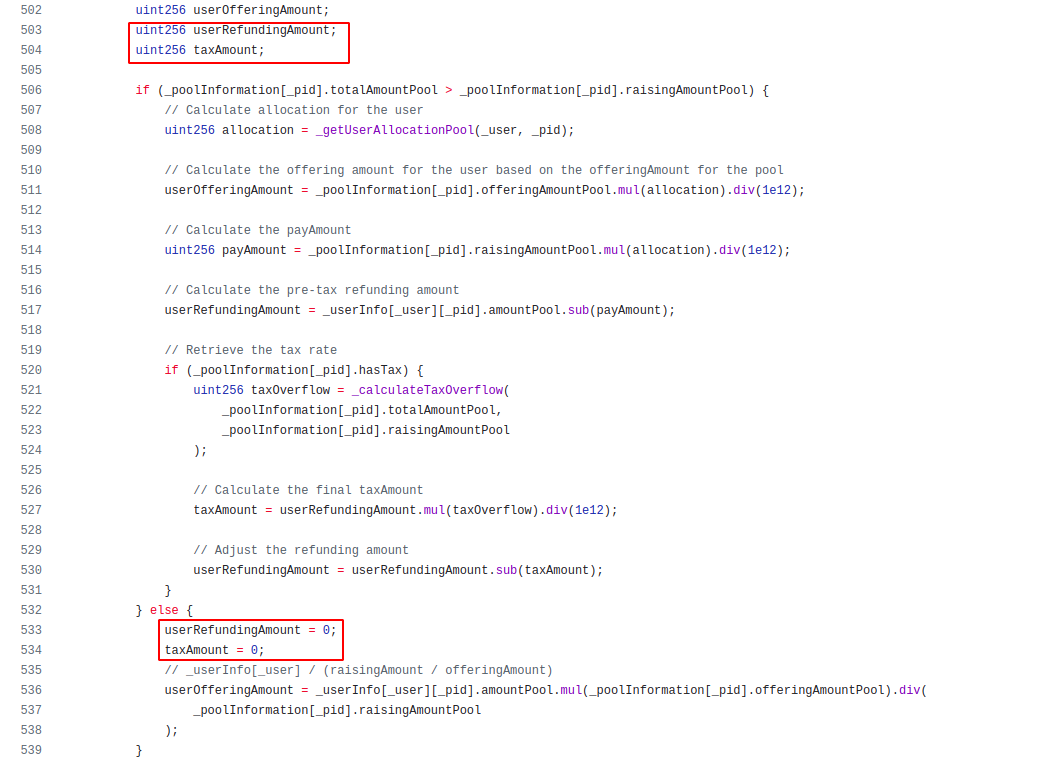
As userRefundingAmount and taxAmountare uint256, they are already initialized to 0. userRefundingAmount = 0 reassigns the 0 to userRefundingAmount which wastes gas.
BVSS
Recommendation
It is recommended to not reinitialize the suggested local variables in order to reduce gas costs.
Remediation Plan
ACKNOWLEDGED: The Secta Finance team acknowledged this finding.
References
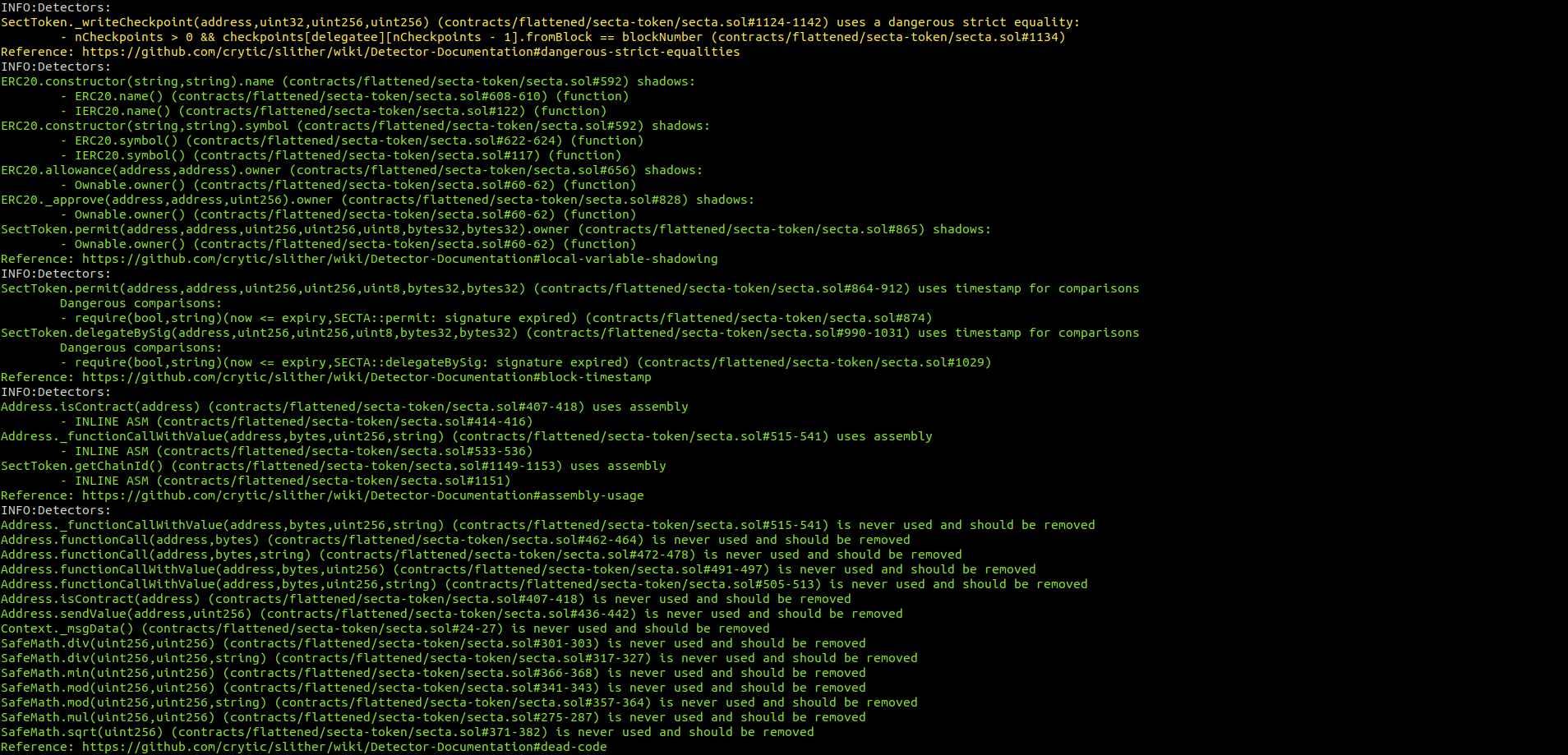
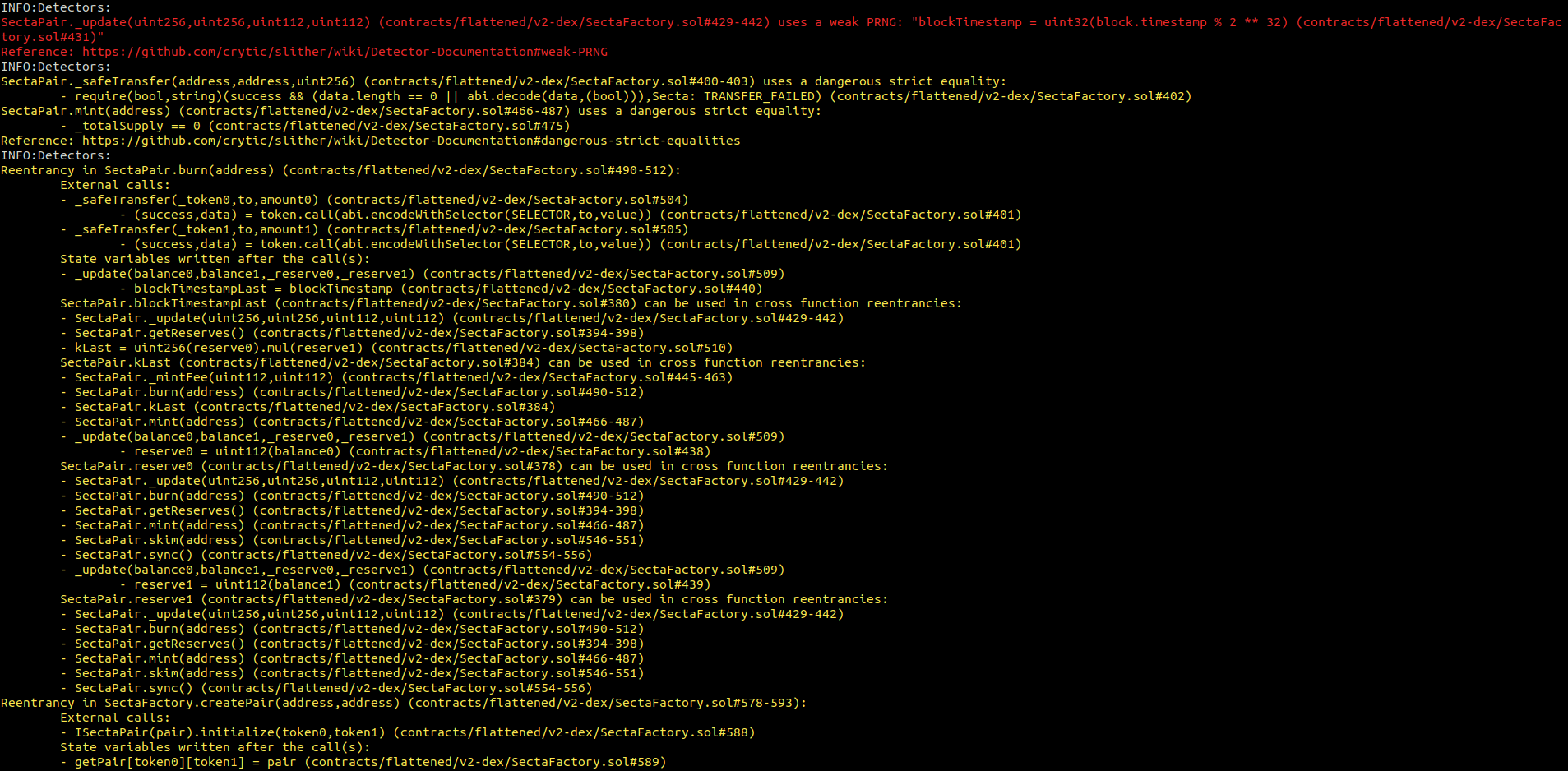
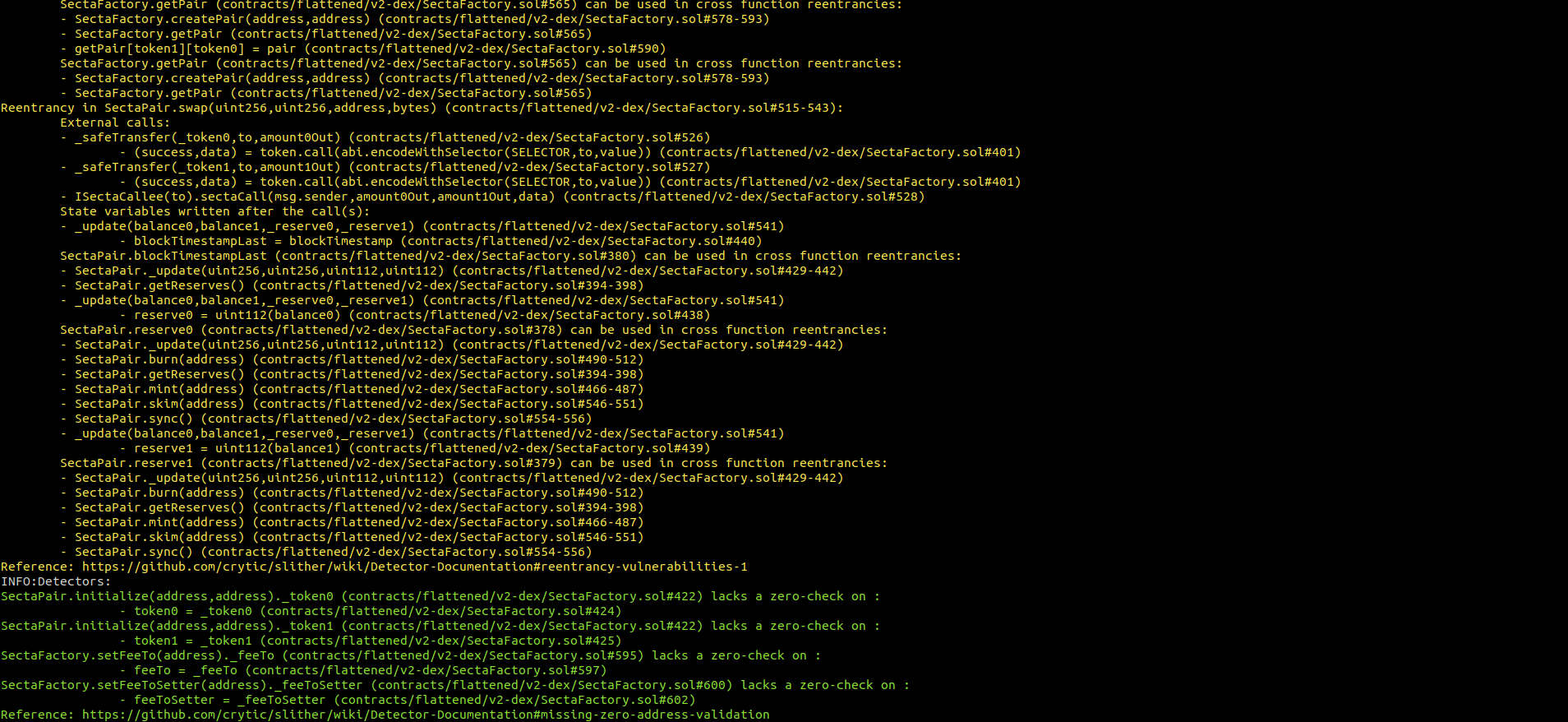
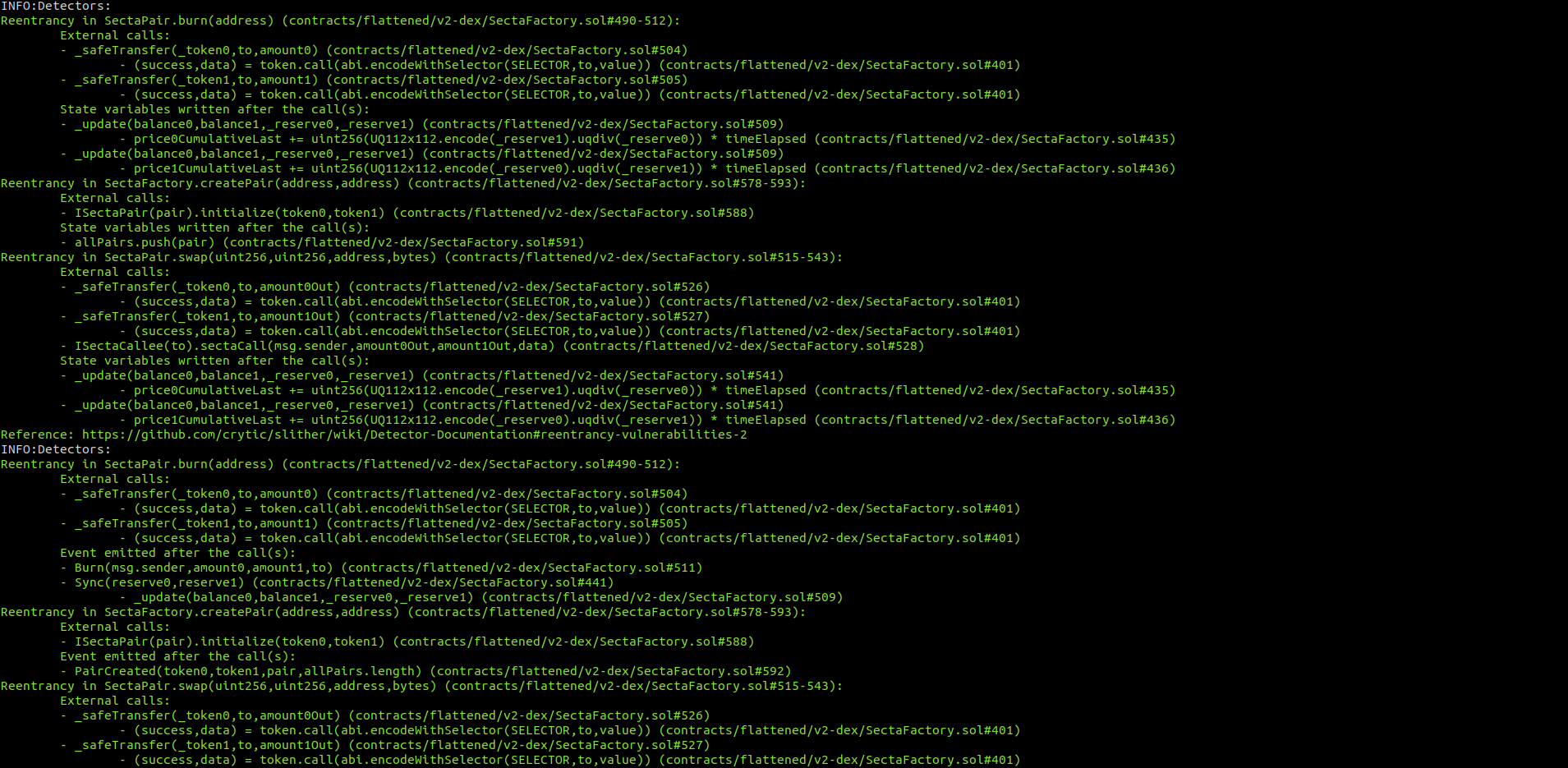
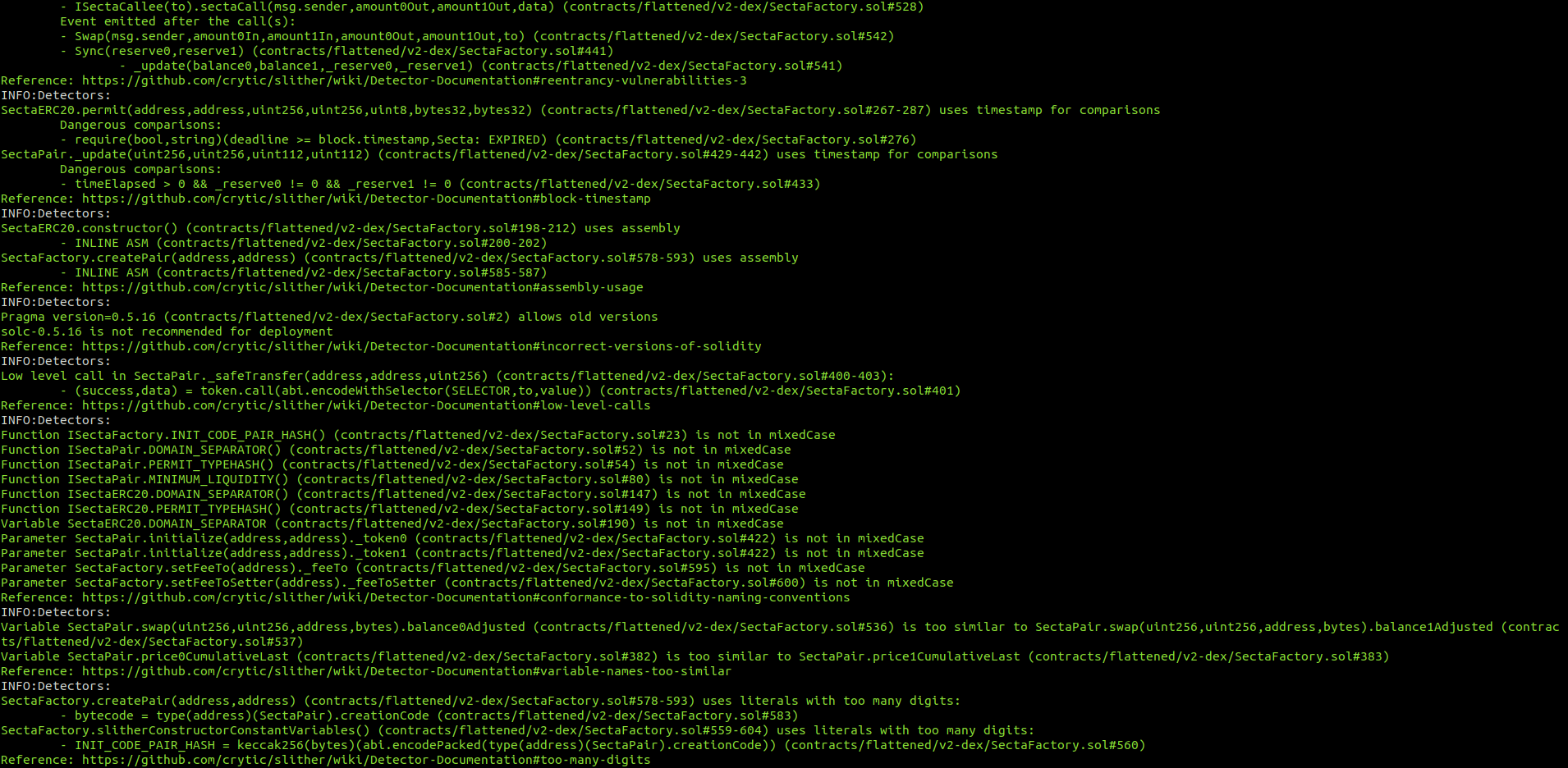
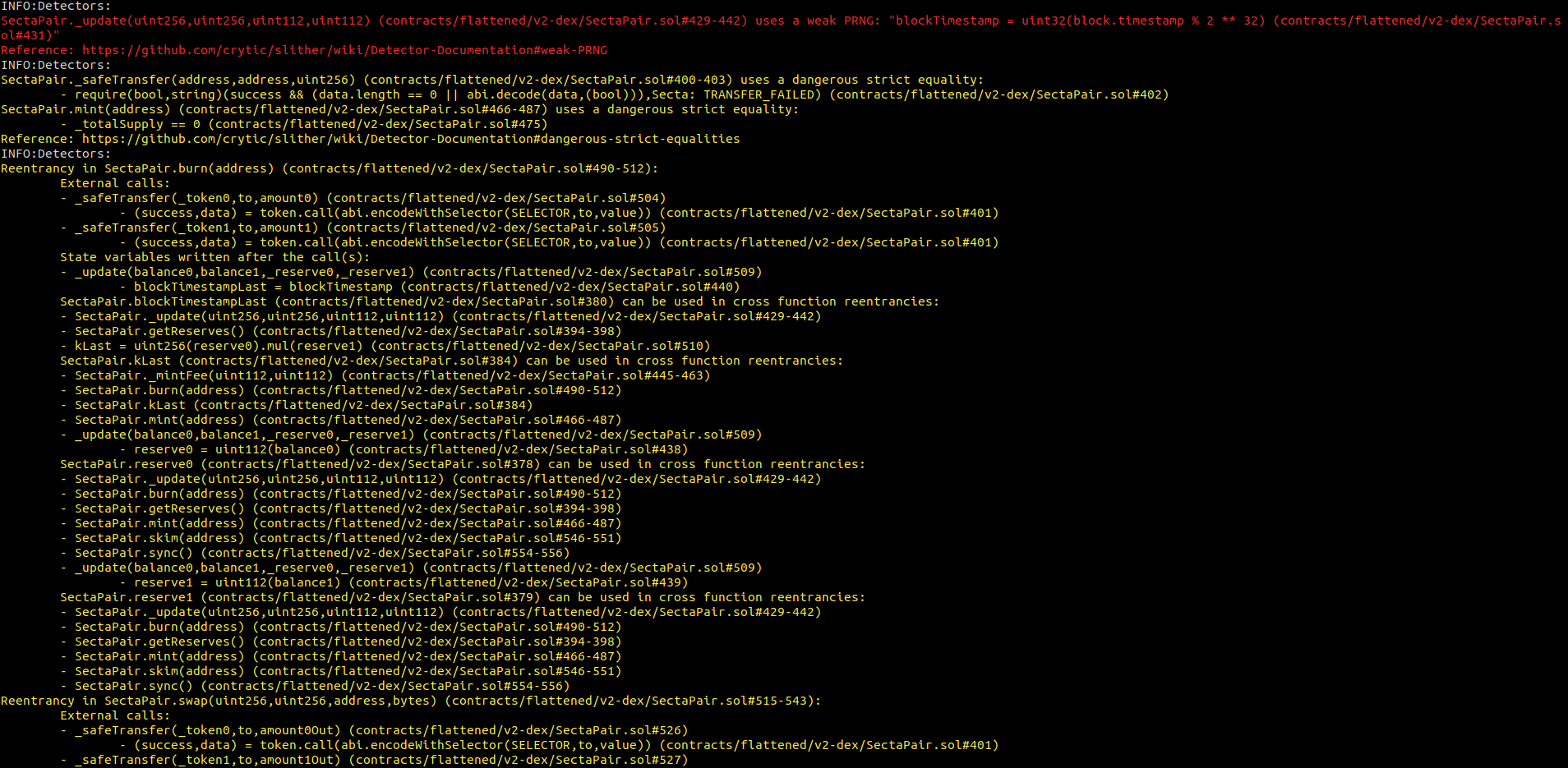
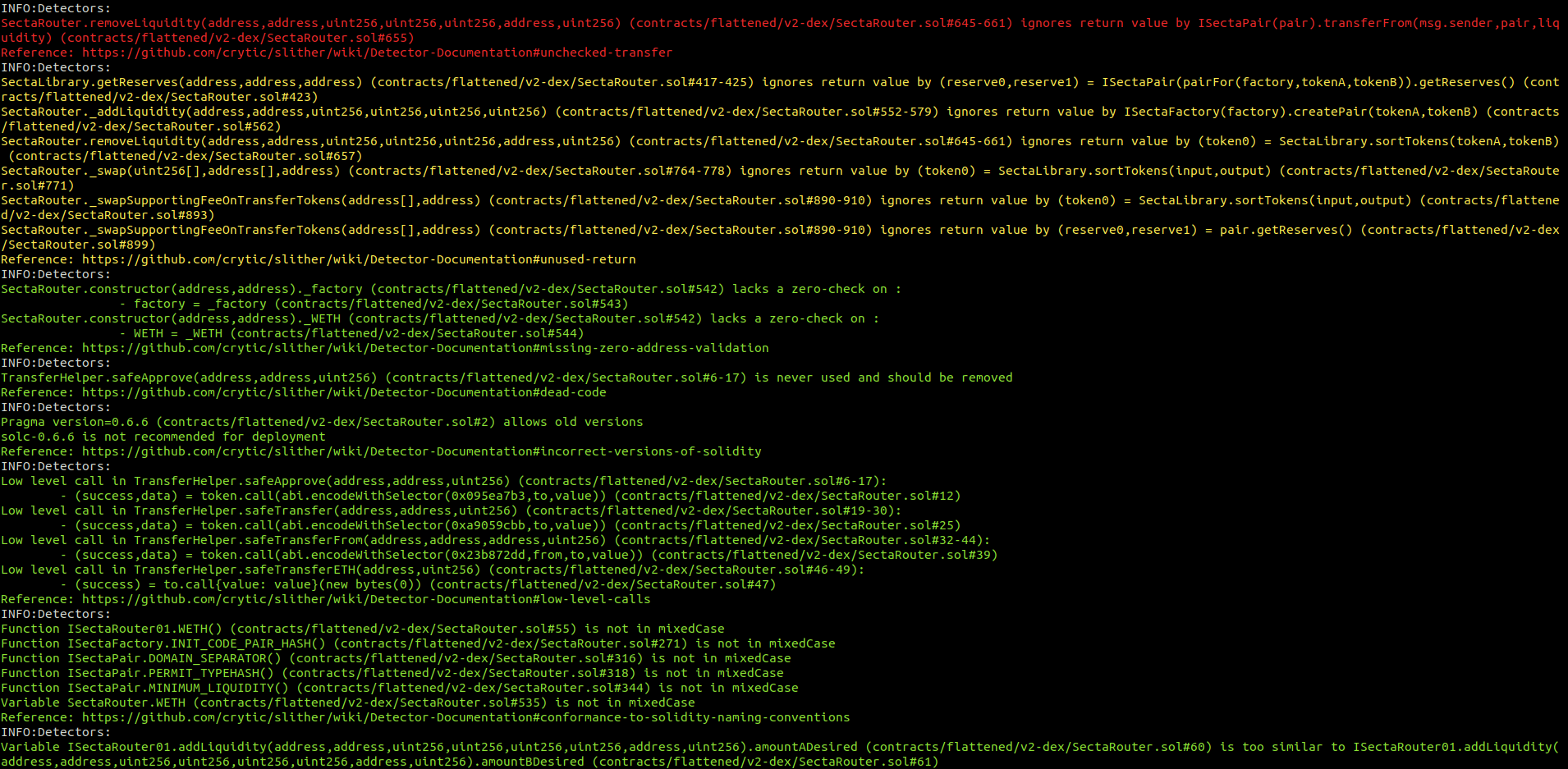
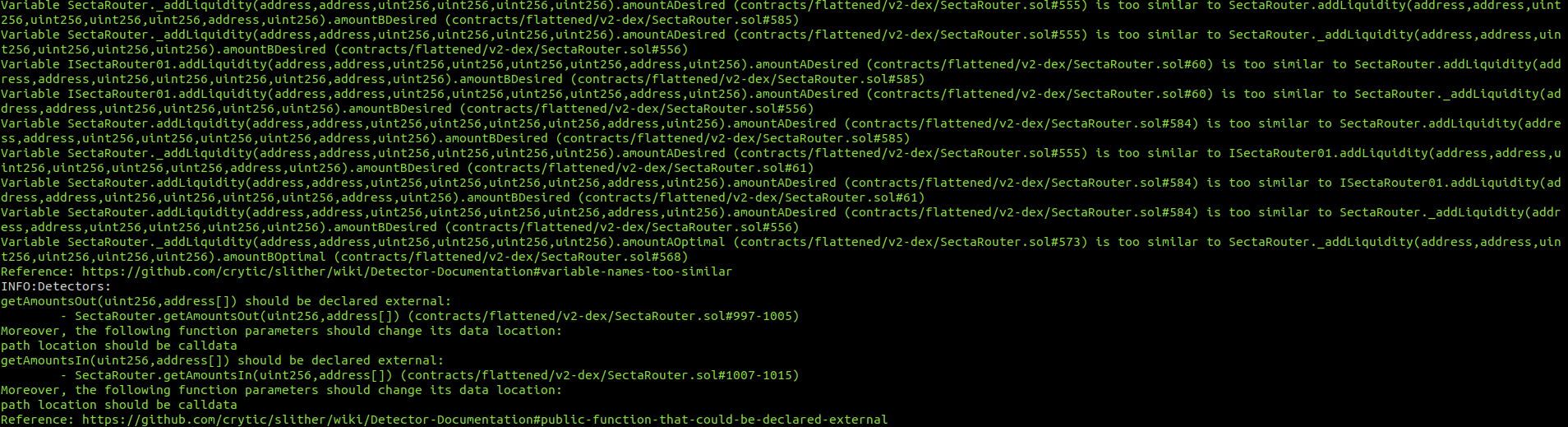
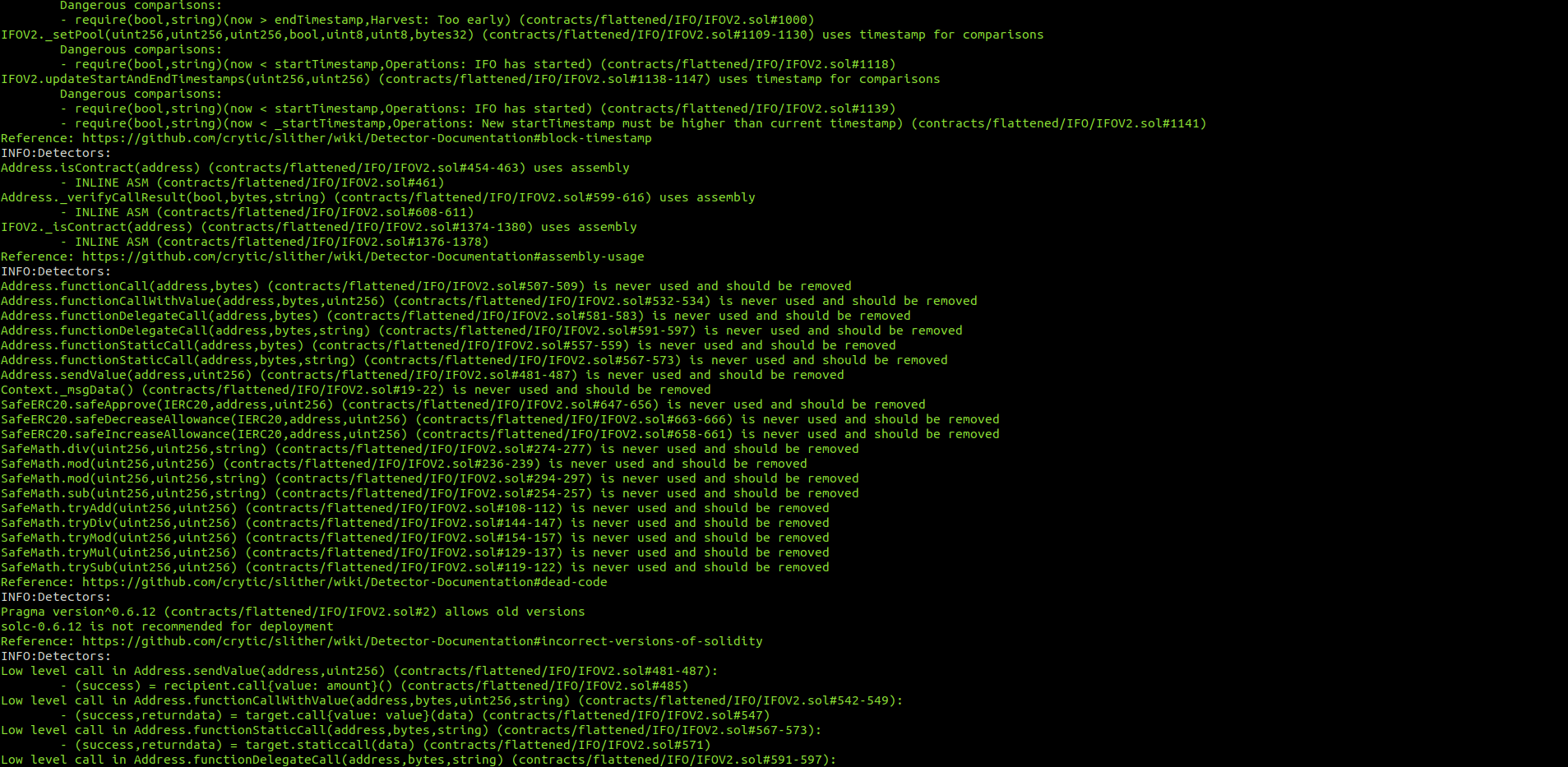
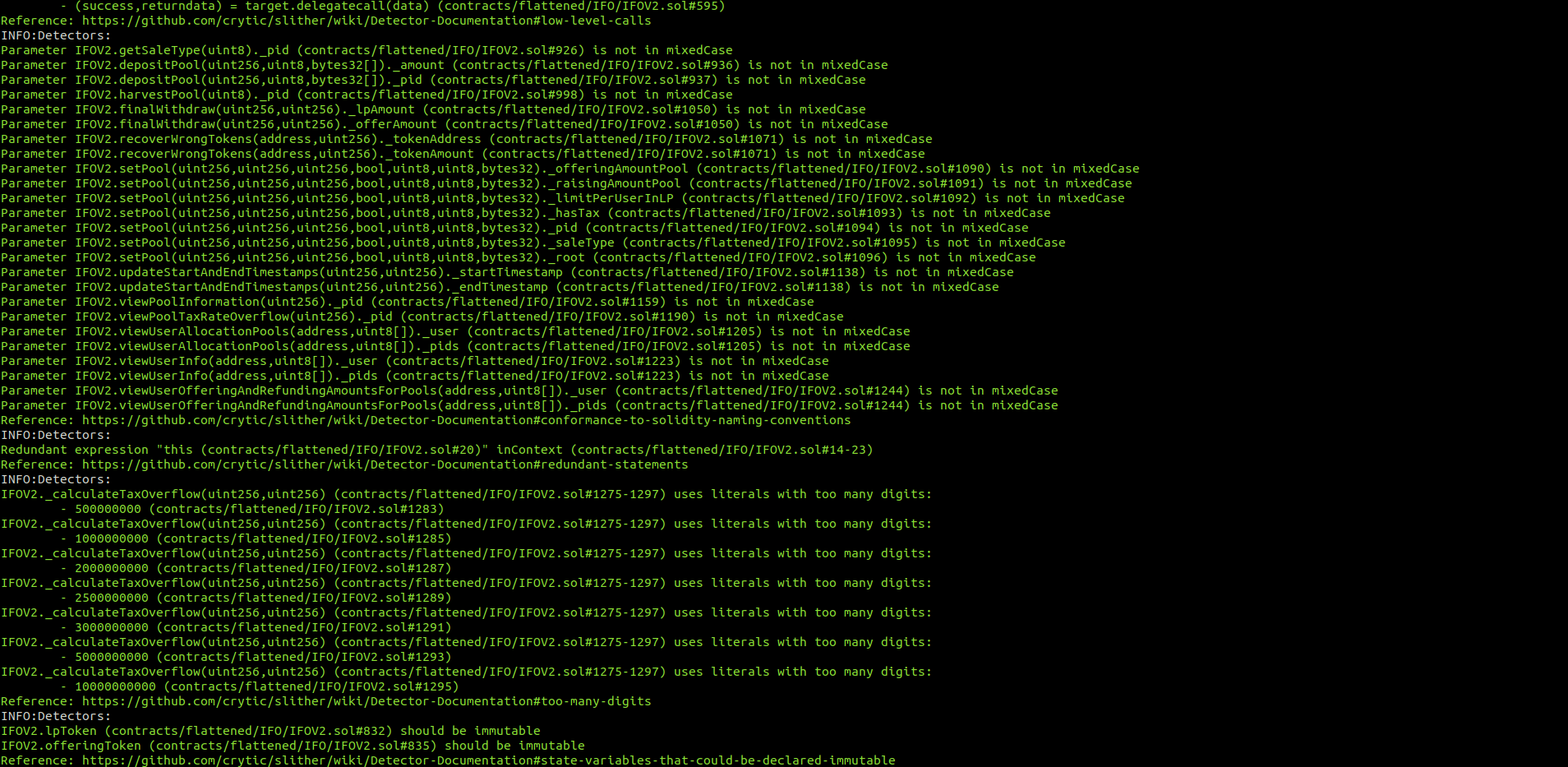
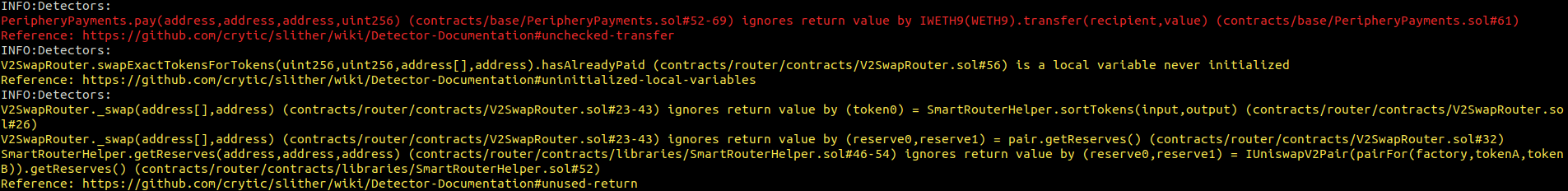
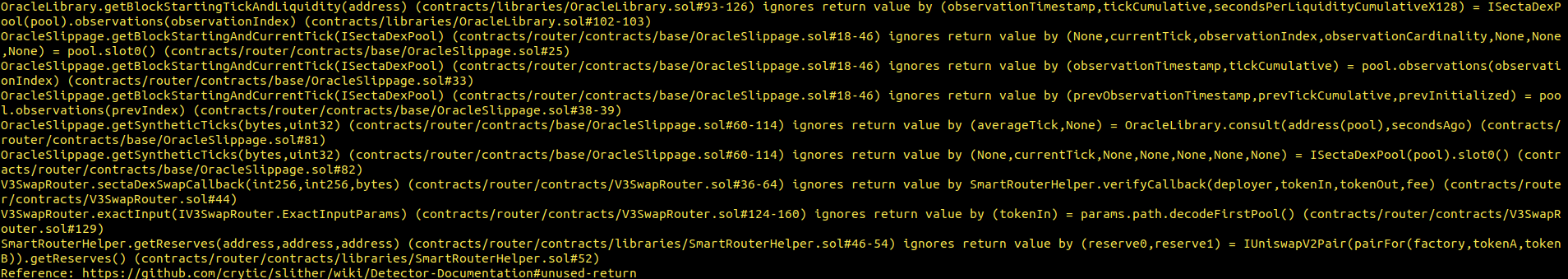
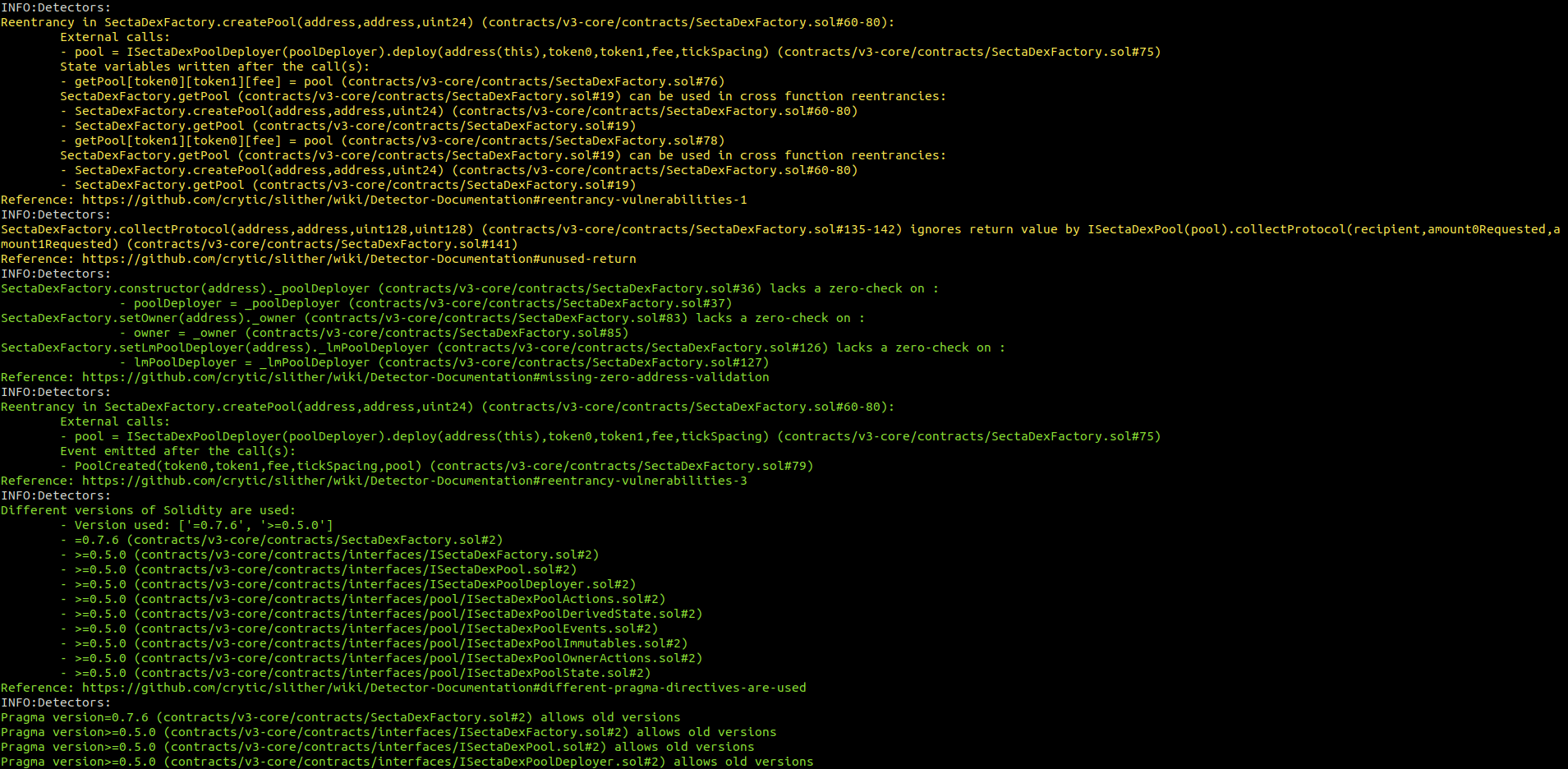
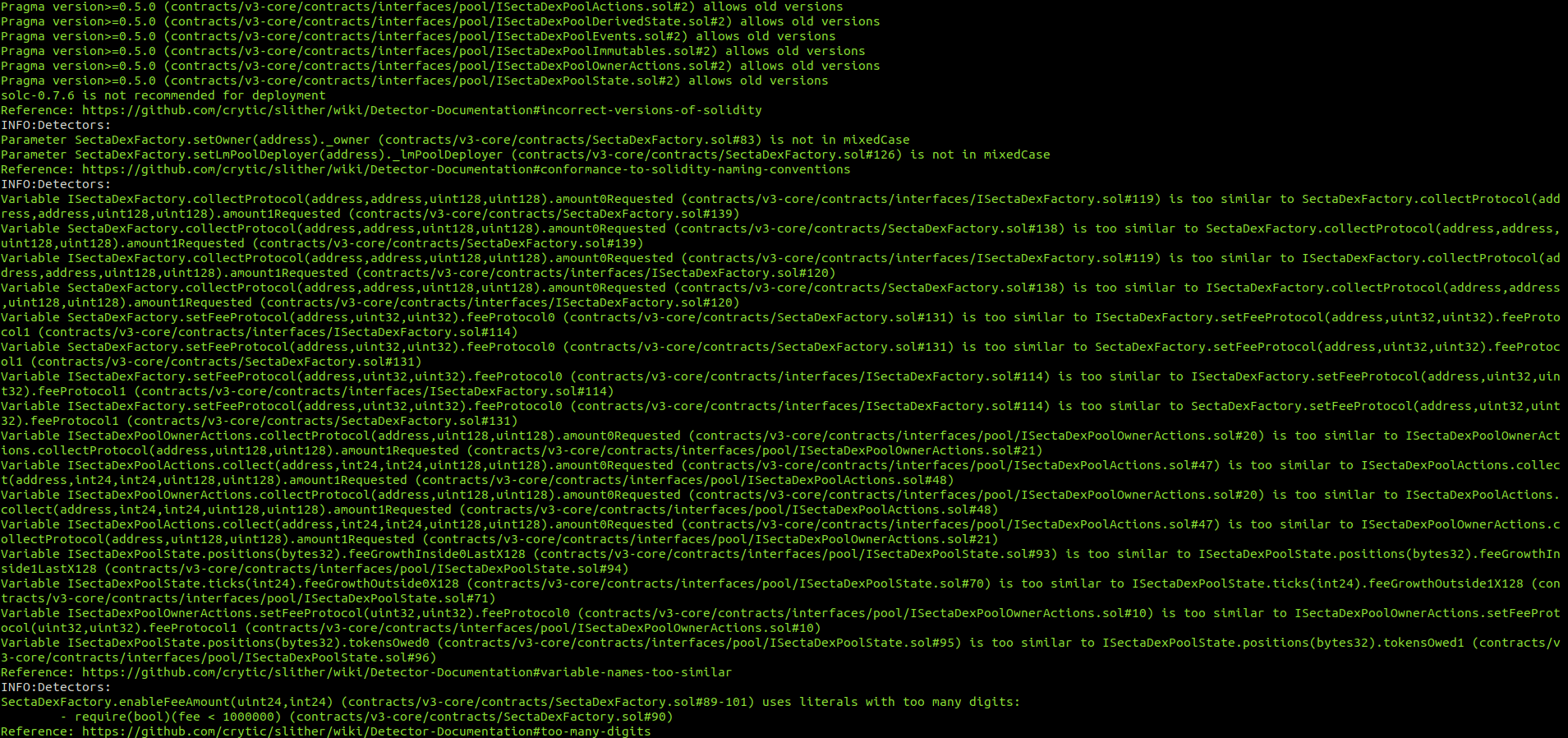
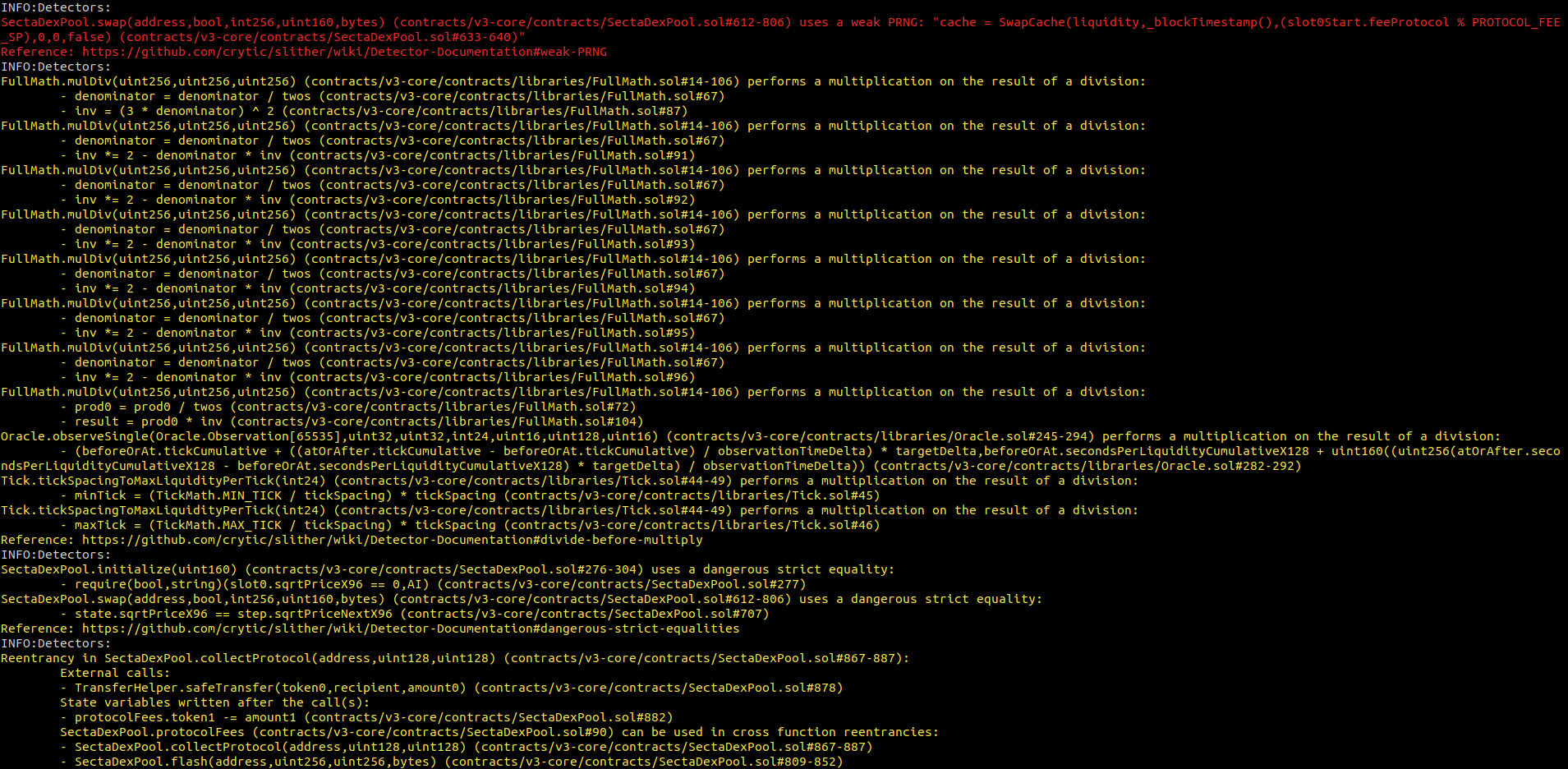
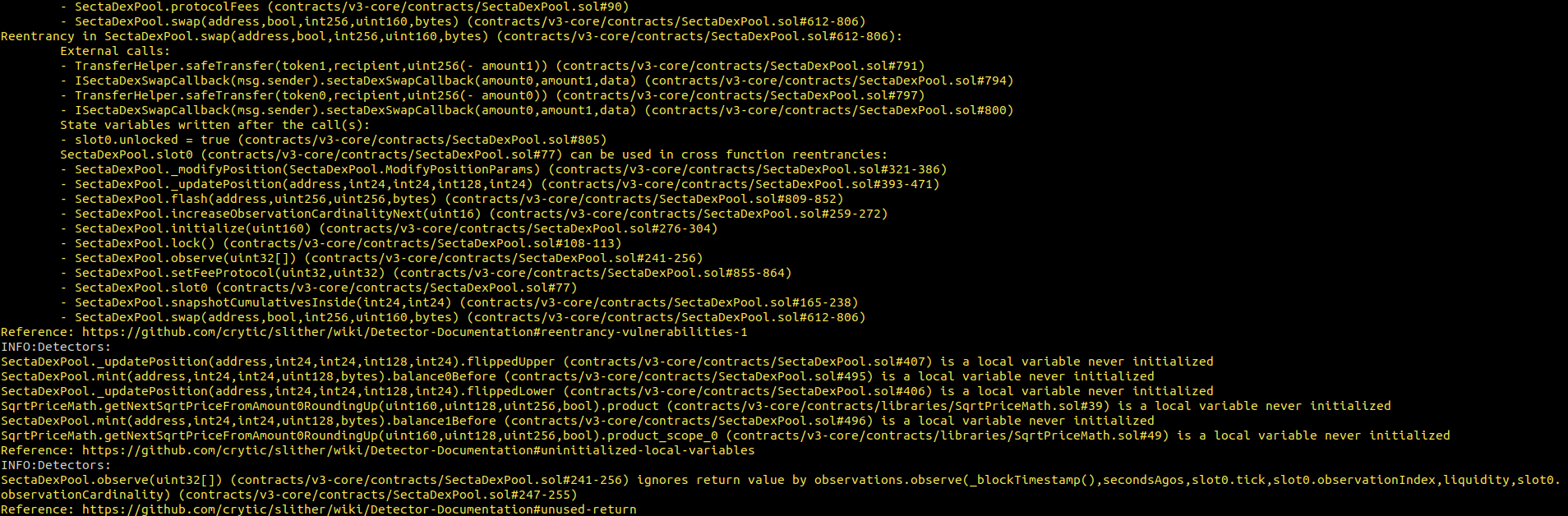
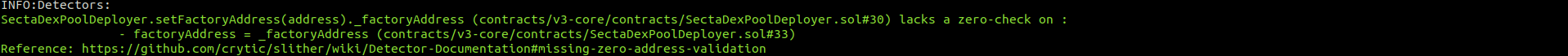
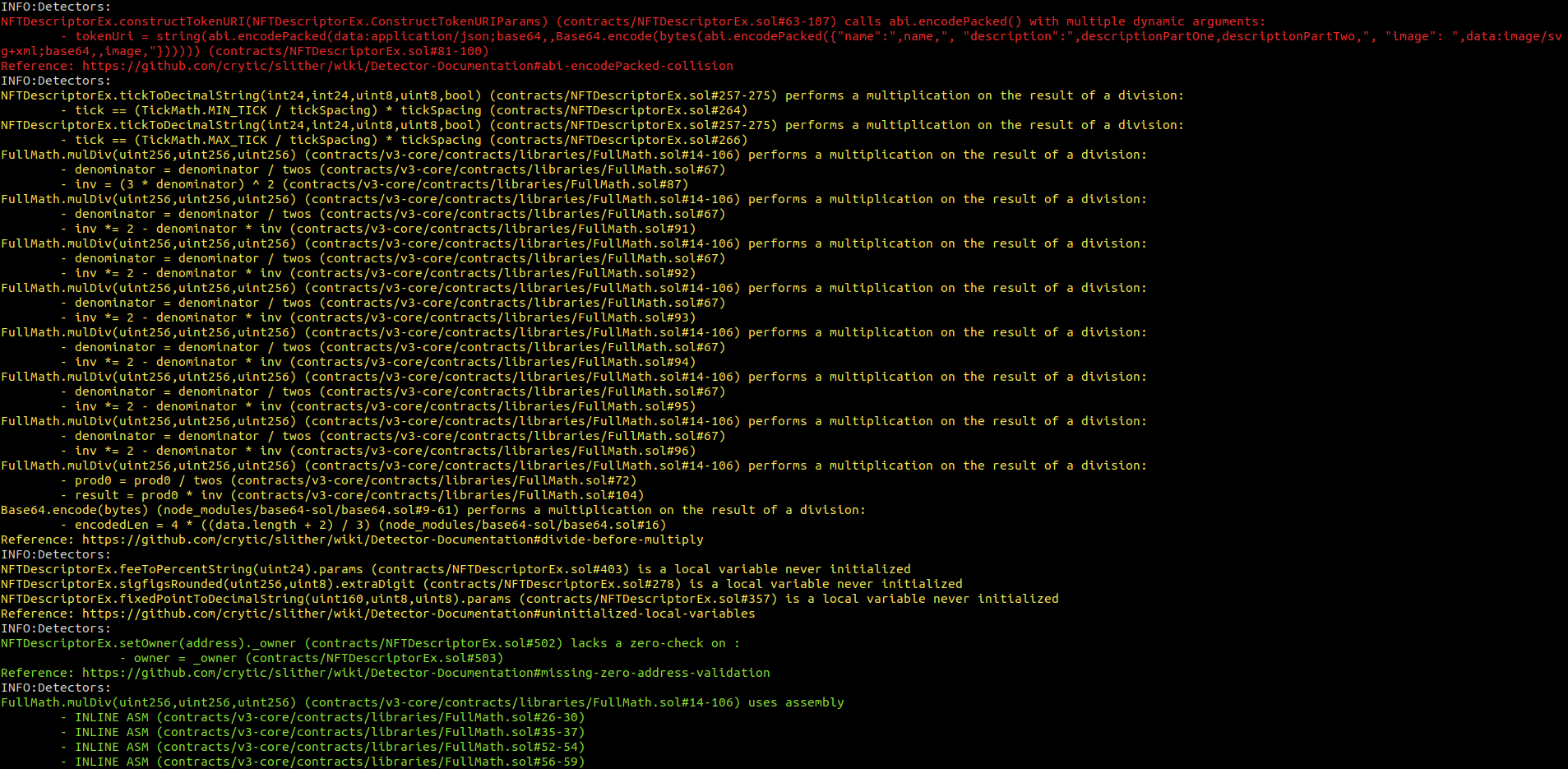
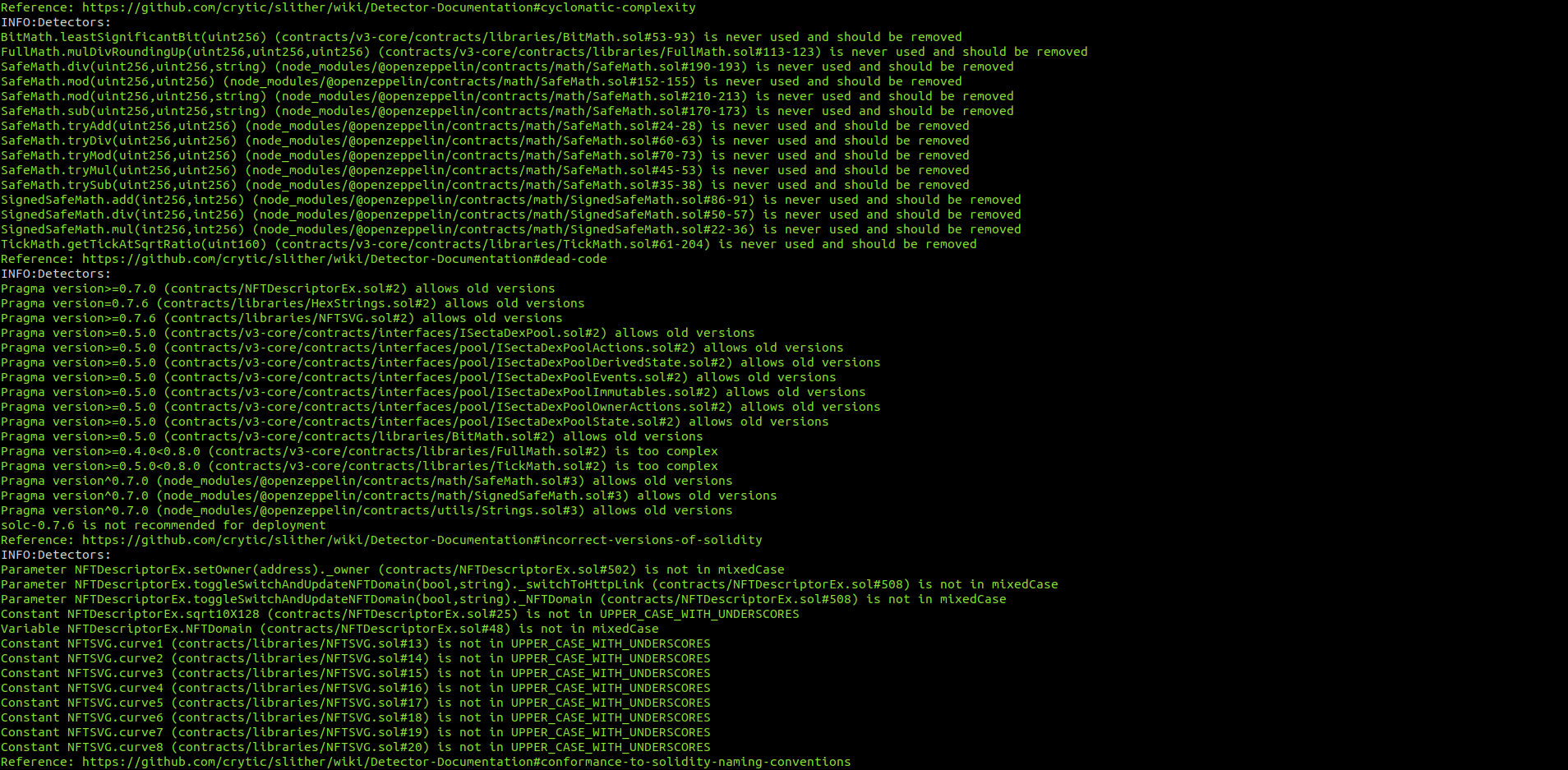
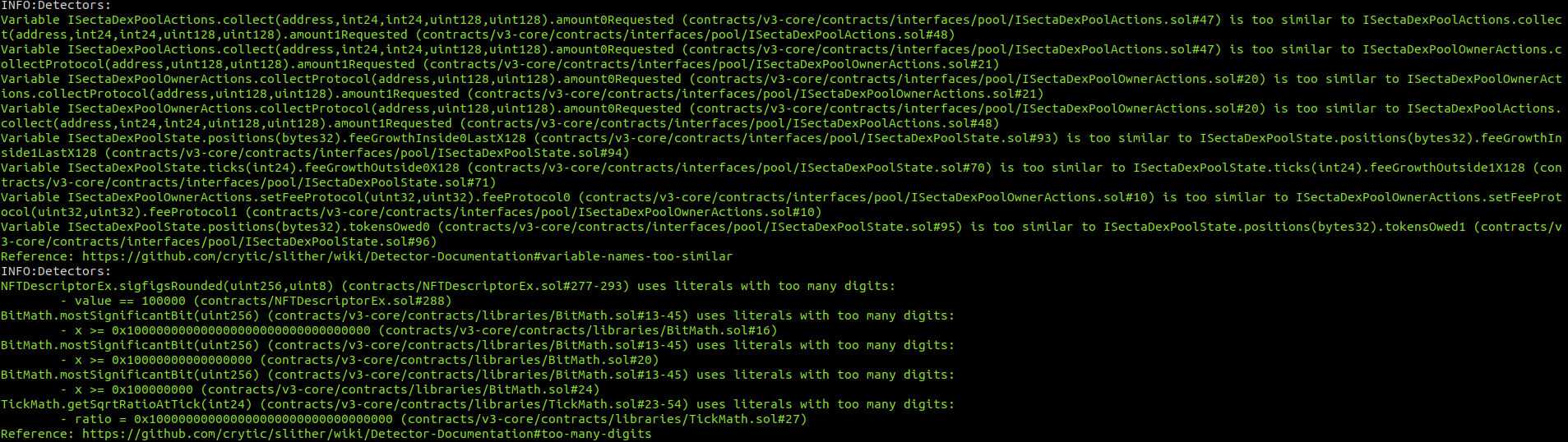
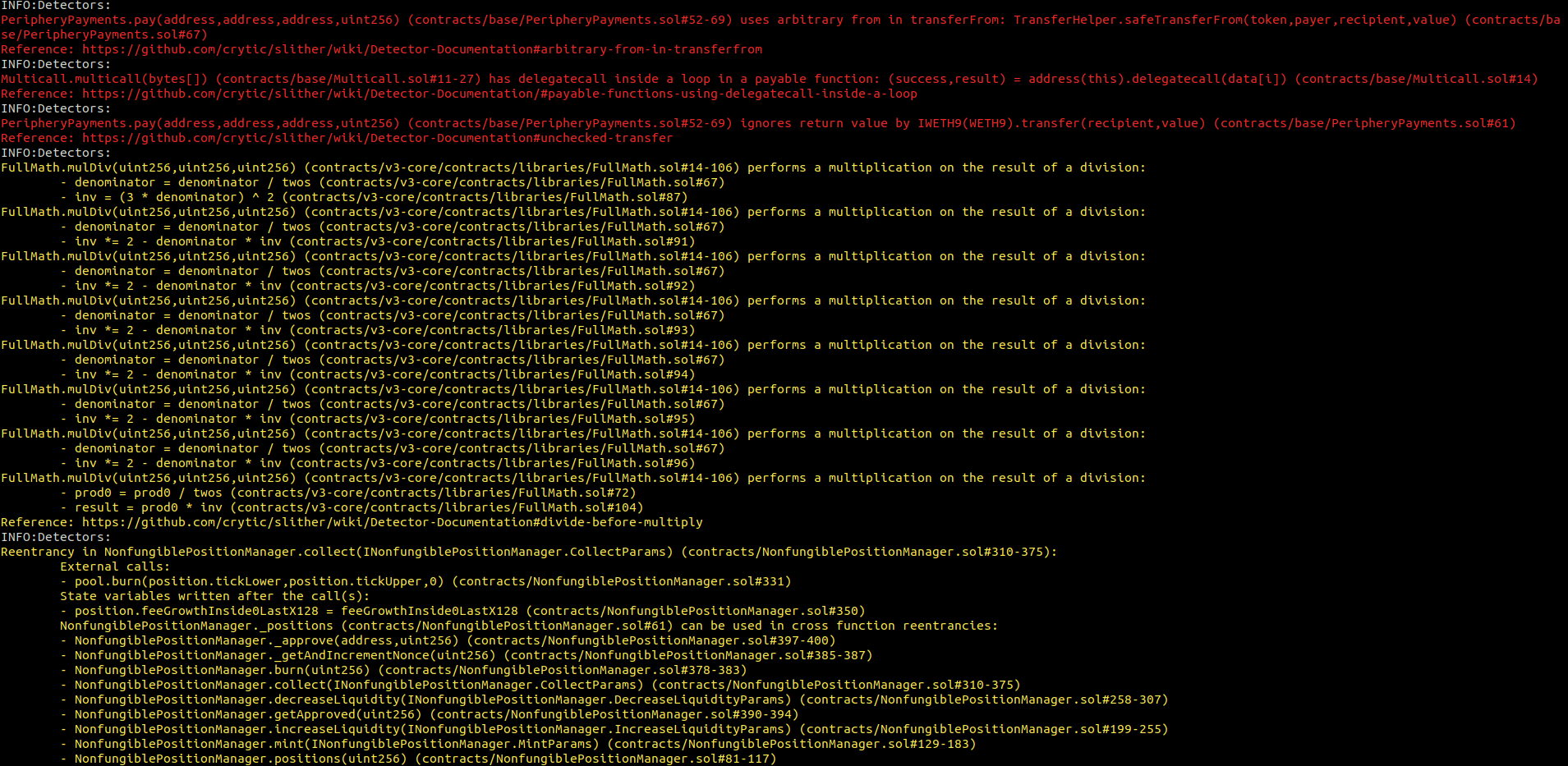
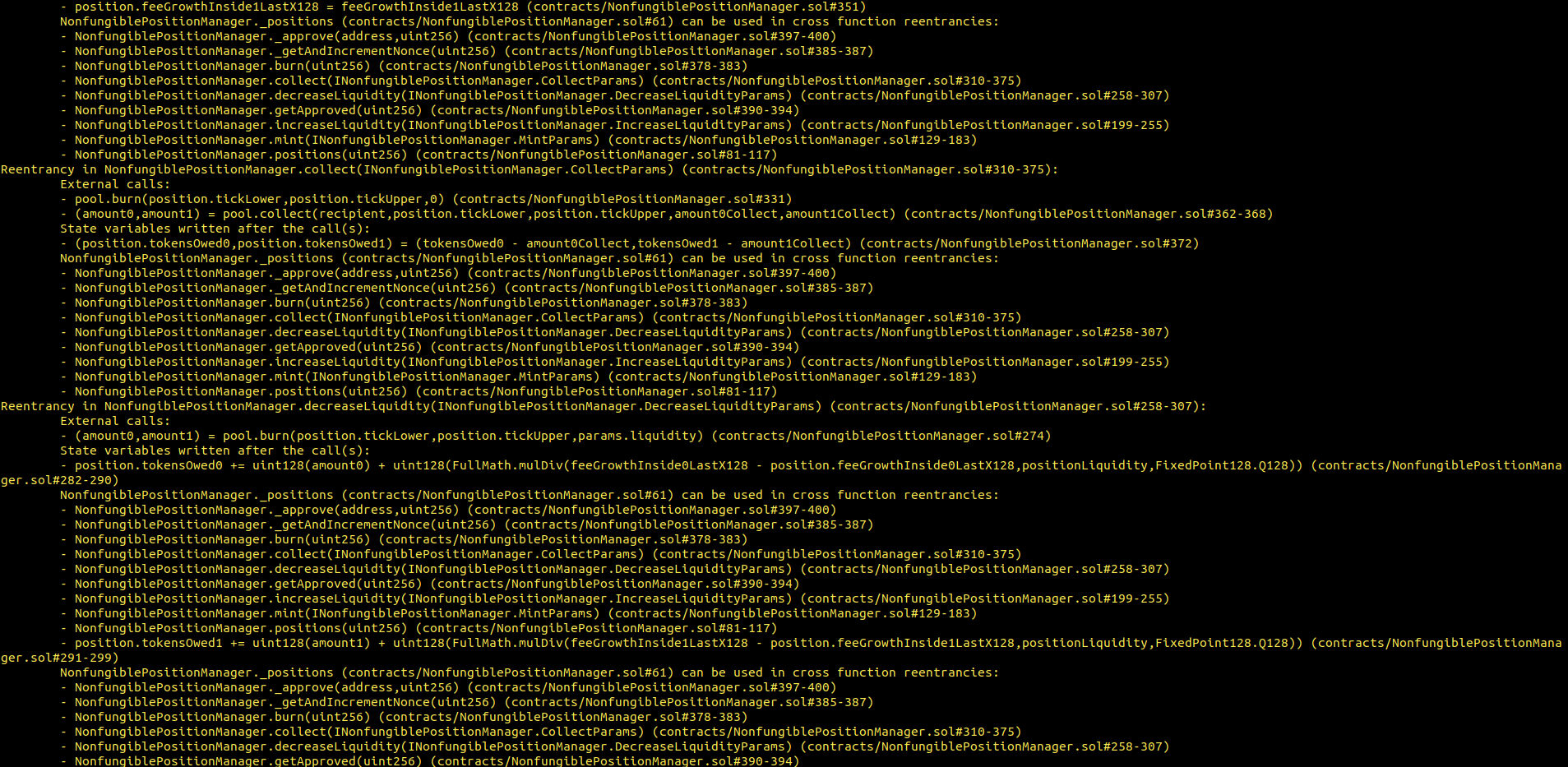
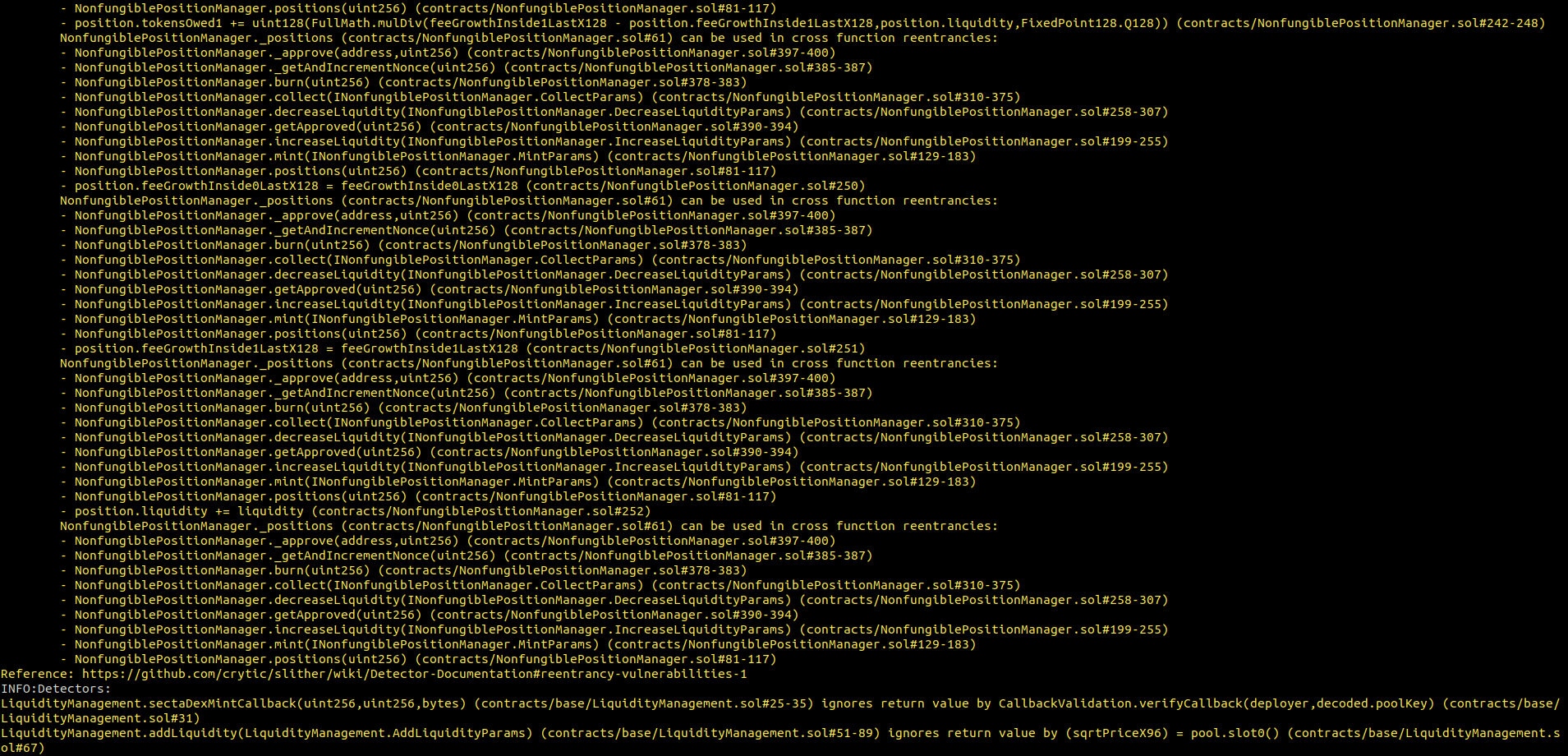
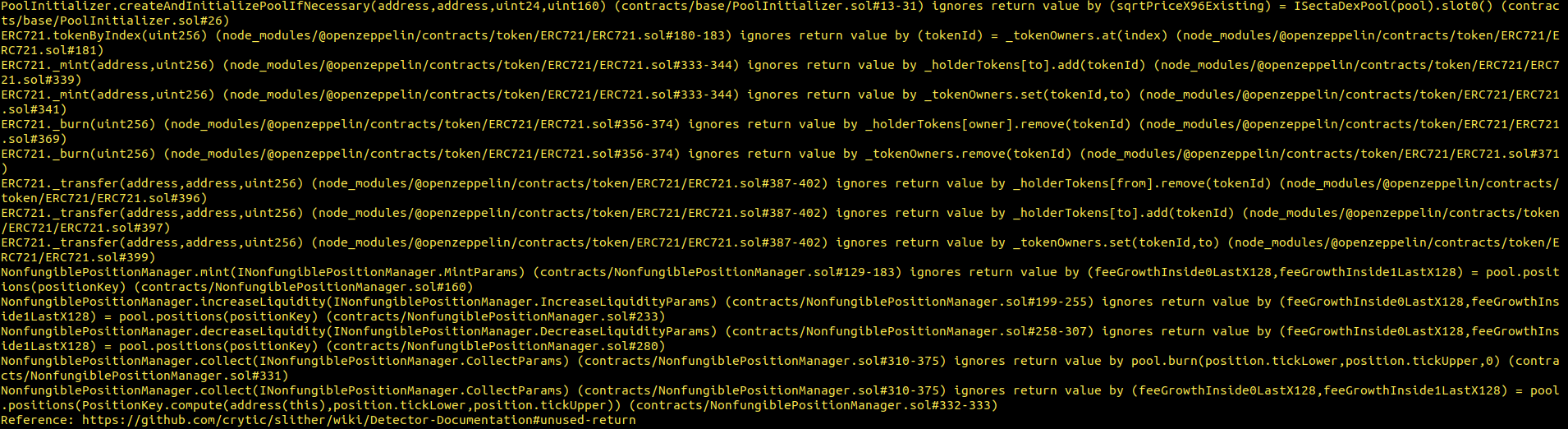
8. Automated Testing
Halborn used automated testing techniques to enhance the coverage of certain areas of the smart contracts in scope. Among the tools used was Slither, a Solidity static analysis framework. After Halborn verified the smart contracts in the repository and was able to compile them correctly into their ABIS and binary format, Slither was run against the contracts. This tool can statically verify mathematical relationships between Solidity variables to detect invalid or inconsistent usage of the contracts' APIs across the entire code-base.
SectToken.sol
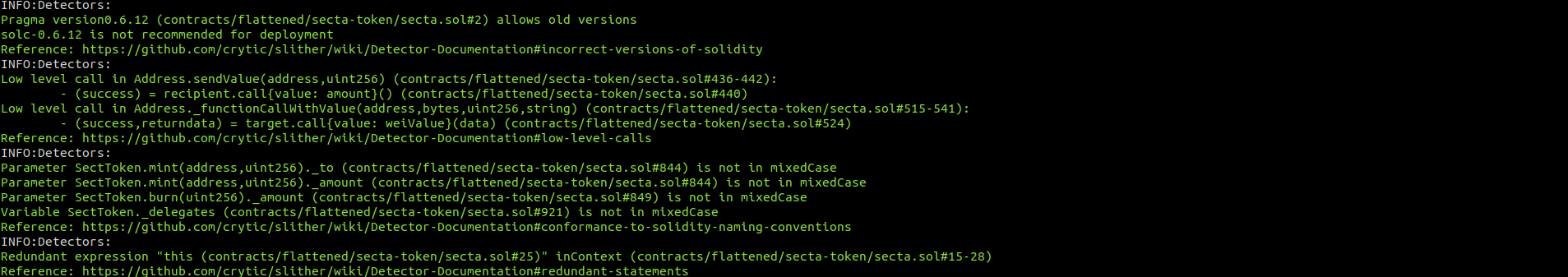
SectaERC20.sol
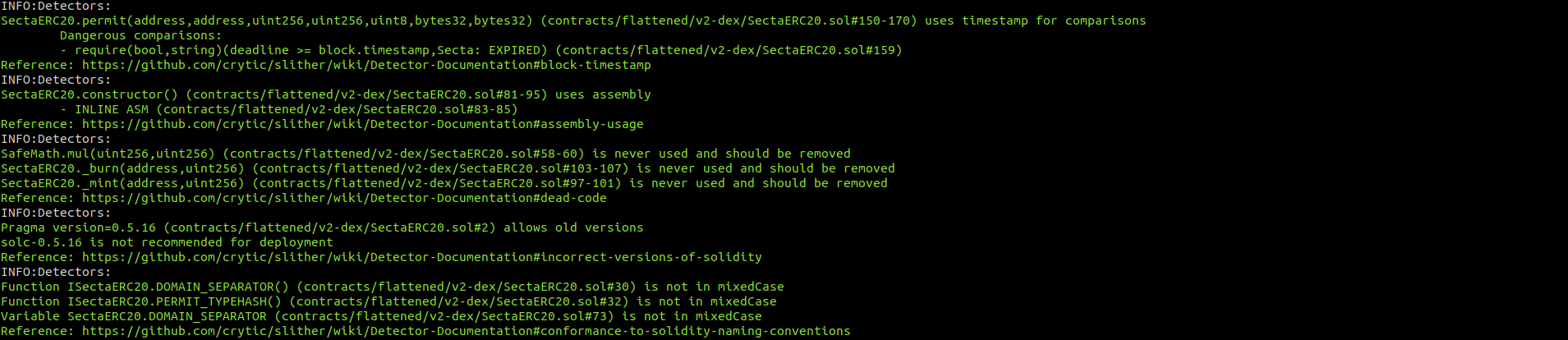
SectaFactory.sol
SectaPair.sol

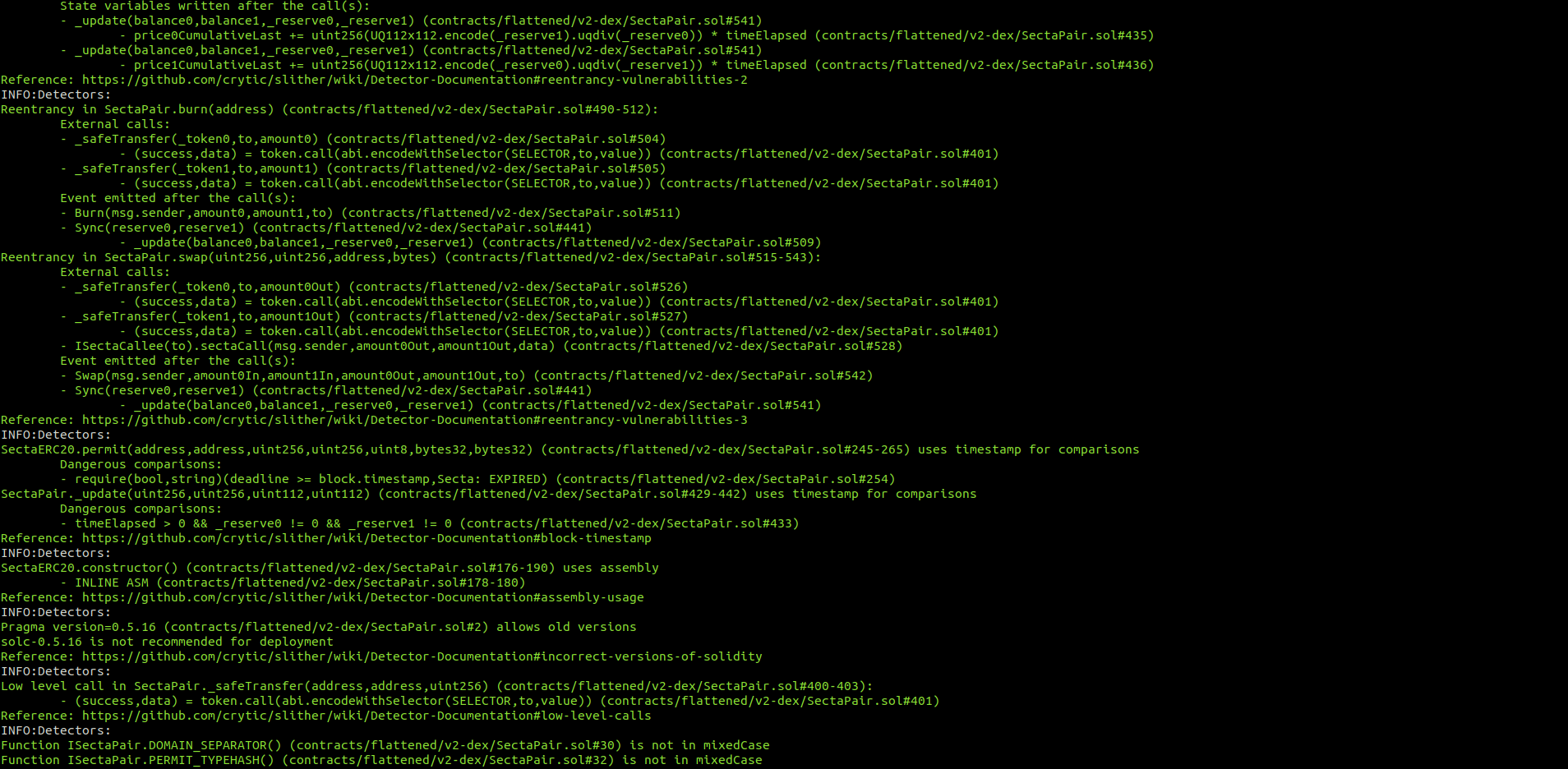
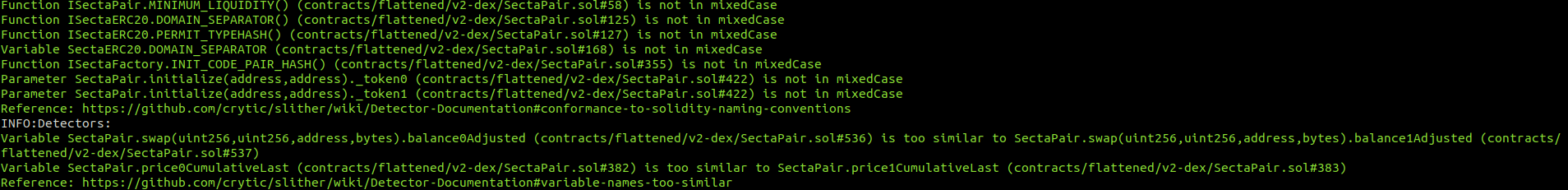
SectaRouter.sol
IFOV2.sol

SmartRouter.sol
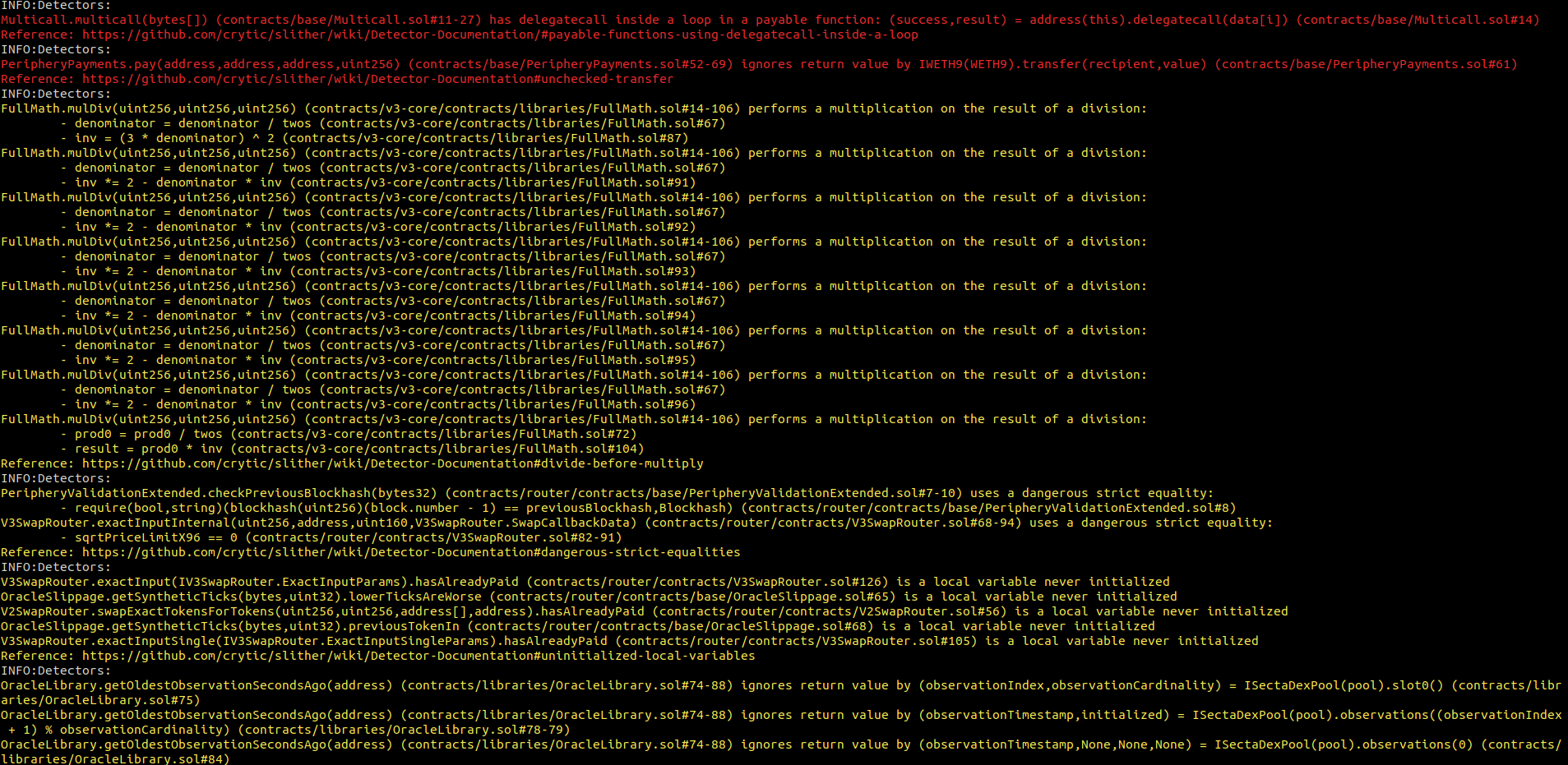

V2SwapRouter.sol
V3SwapRouter.sol
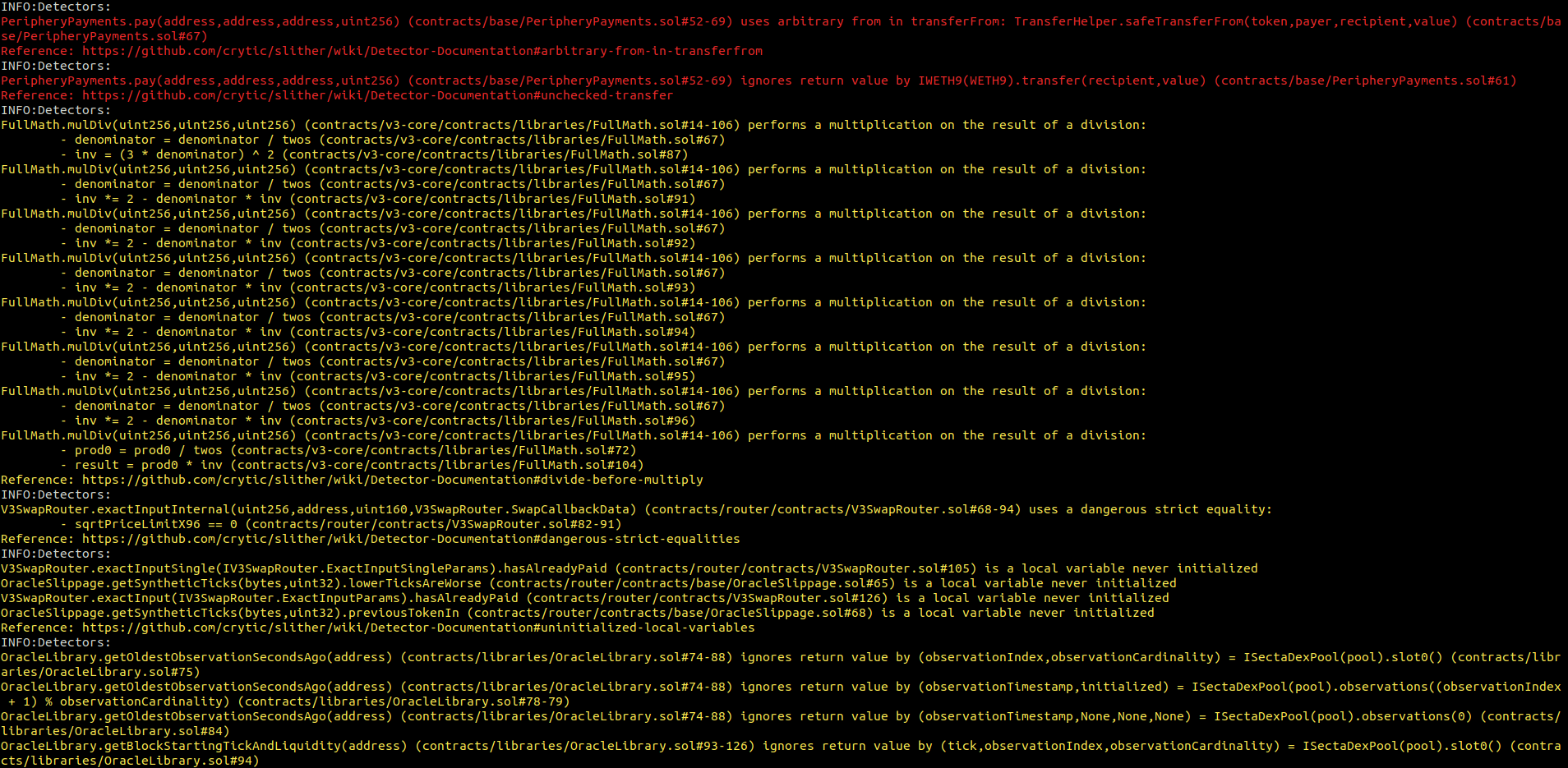
SectaDexFactory.sol
SectaDexPool.sol
SectaDexPoolDeployer.sol
NFTDescriptorEx.sol
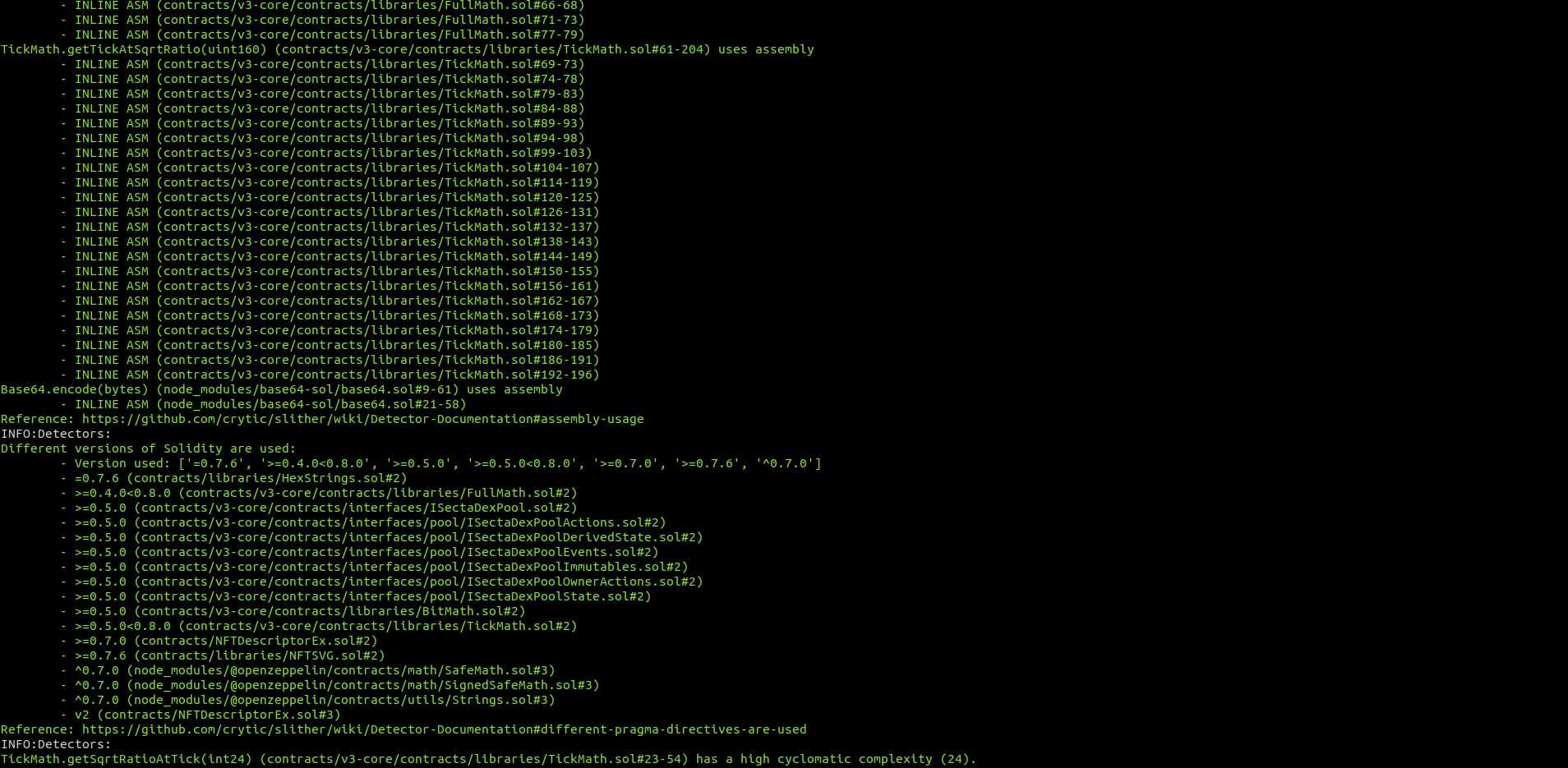
NonfungiblePositionManager.sol

SwapRouter.sol

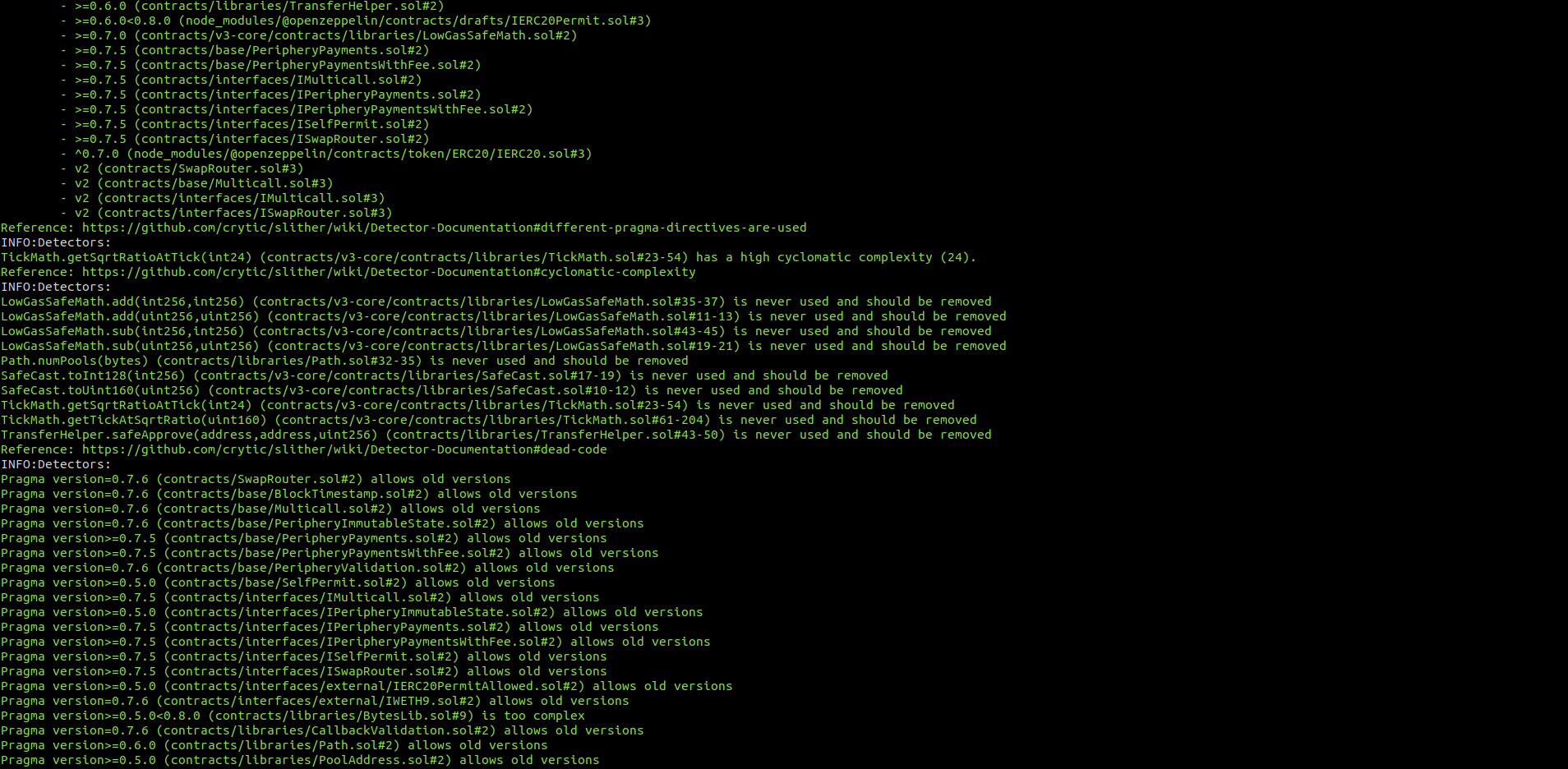
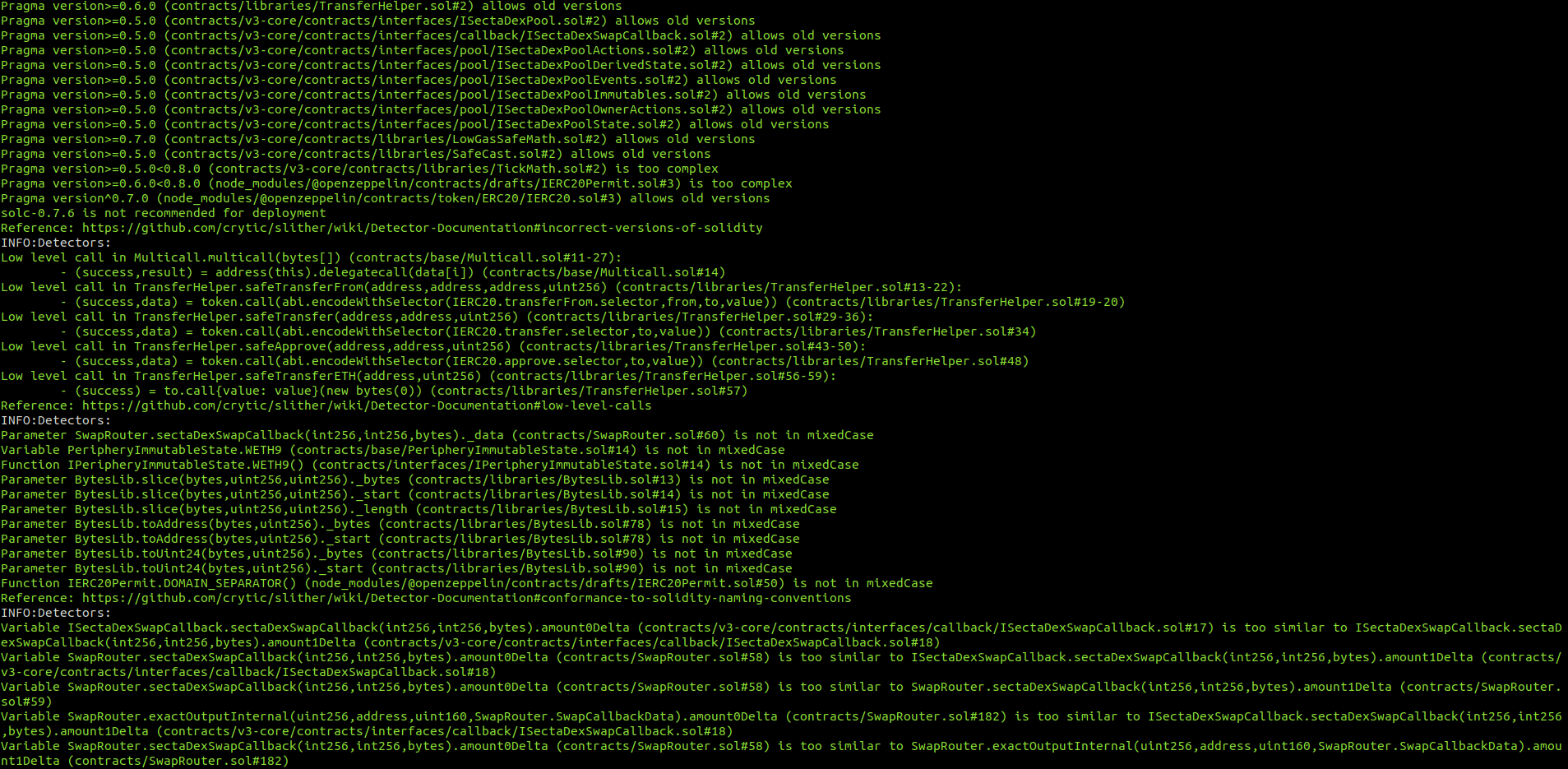
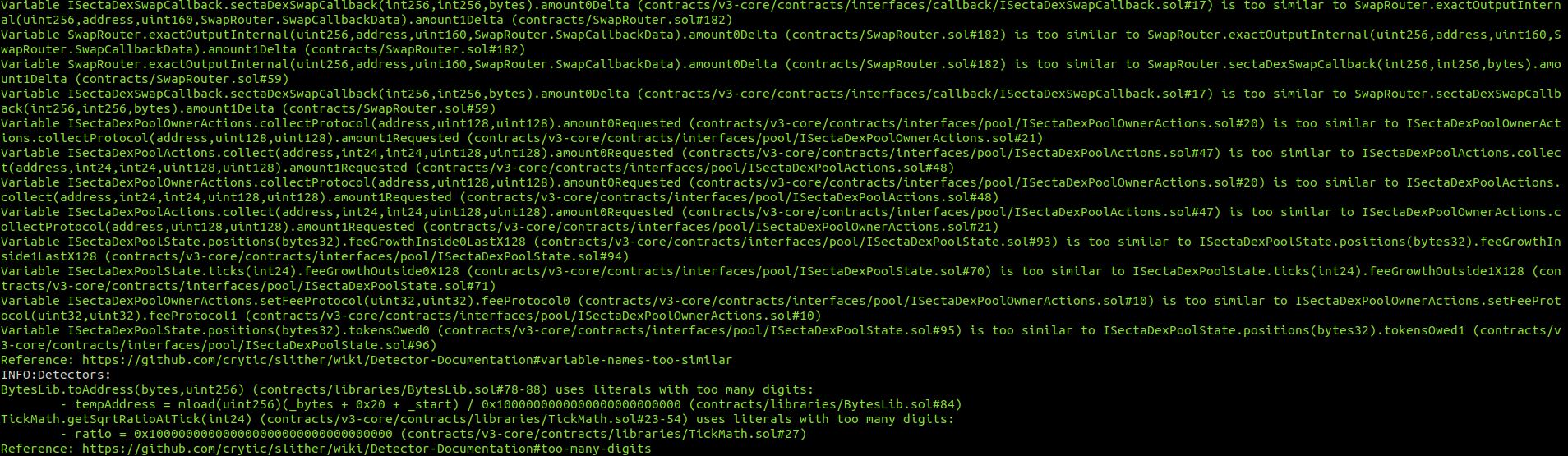
The weak PRNG flagged by Slither is a false positive.
All the reentrancies flagged by Slither were checked individually and are all false positives.
No major issues were found by Slither.
Halborn strongly recommends conducting a follow-up assessment of the project either within six months or immediately following any material changes to the codebase, whichever comes first. This approach is crucial for maintaining the project’s integrity and addressing potential vulnerabilities introduced by code modifications.
Table of Contents
- 1. Introduction
- 2. Assessment summary
- 3. Test approach and methodology
- 4. Risk methodology
- 5. Scope
- 6. Assessment summary & findings overview
- 7. Findings & Tech Details
- 7.1 Centralization risk in ifov2.finalwithdraw() function
- 7.2 Erc20 permits are vulnerable to griefing via frontrunning
- 7.3 Direct usage of ecrecover allows signature malleability
- 7.4 Missing disableinitializers() call
- 7.5 Floating pragma
- 7.6 Unoptimized loops
- 7.7 Lack of a double-step transferownership() pattern
- 7.8 Unneeded initialization of uint256 variables to 0
- 8. Automated Testing
// Download the full report
* Use Google Chrome for best results
** Check "Background Graphics" in the print settings if needed
