Prepared by:
HALBORN
Last Updated 05/27/2025
Date of Engagement: April 28th, 2025 - May 1st, 2025
100% of all REPORTED Findings have been addressed
All findings
7
Critical
0
High
0
Medium
0
Low
2
Informational
5
Aria Protocol engaged Halborn to conduct a security assessment on their smart contracts beginning on April 28th, 2025 and ending on May 1st, 2025. The security assessment was scoped to the smart contracts provided to Halborn. Commit hashes and further details can be found in the Scope section of this report.
The Aria Protocol codebase in scope mainly consists of smart contracts for creating and managing intellectual property (IP) vaults that enable the tokenization and fractionalization of IP assets, with support for fundraising and whitelist-based distribution mechanisms.
Halborn was provided 4 days for the engagement and assigned 1 full-time security engineer to review the security of the smart contracts in scope. The engineer is a blockchain and smart contract security expert with advanced penetration testing and smart contract hacking skills, and deep knowledge of multiple blockchain protocols.
The purpose of the assessment is to:
Identify potential security issues within the smart contracts.
Ensure that smart contract functionality operates as intended.
In summary, Halborn identified some improvements to reduce the likelihood and impact of risks, which were partially addressed by the Aria Protocol team. The main ones are the following:
Add the _checkAndUpdateState() call at the beginning of both claimFractionalTokens() implementations.
Consider implementing proper validation of the USDC address.
Consider implementing a registry mechanism at the factory level to track and validate token identifiers.
All addressed findings have been consolidated and incorporated into version v1.0.5, available in the following commit: https://github.com/AriaProtocol/main-contracts/tree/83cbf9a4b2b67f54f524a7daae33e7a49efb2860.
Halborn performed a combination of manual review of the code and automated security testing to balance efficiency, timeliness, practicality, and accuracy in regard to the scope of this assessment. While manual testing is recommended to uncover flaws in logic, process, and implementation; automated testing techniques help enhance coverage of smart contracts and can quickly identify items that do not follow security best practices.
The following phases and associated tools were used throughout the term of the assessment:
Research into architecture, purpose and use of the platform.
Smart contract manual code review and walkthrough to identify any logic issue.
Thorough assessment of safety and usage of critical Solidity variables and functions in scope that could led to arithmetic related vulnerabilities.
Local testing with custom scripts (Foundry).
Fork testing against main networks (Foundry).
Static analysis of security for scoped contract, and imported functions (Slither).
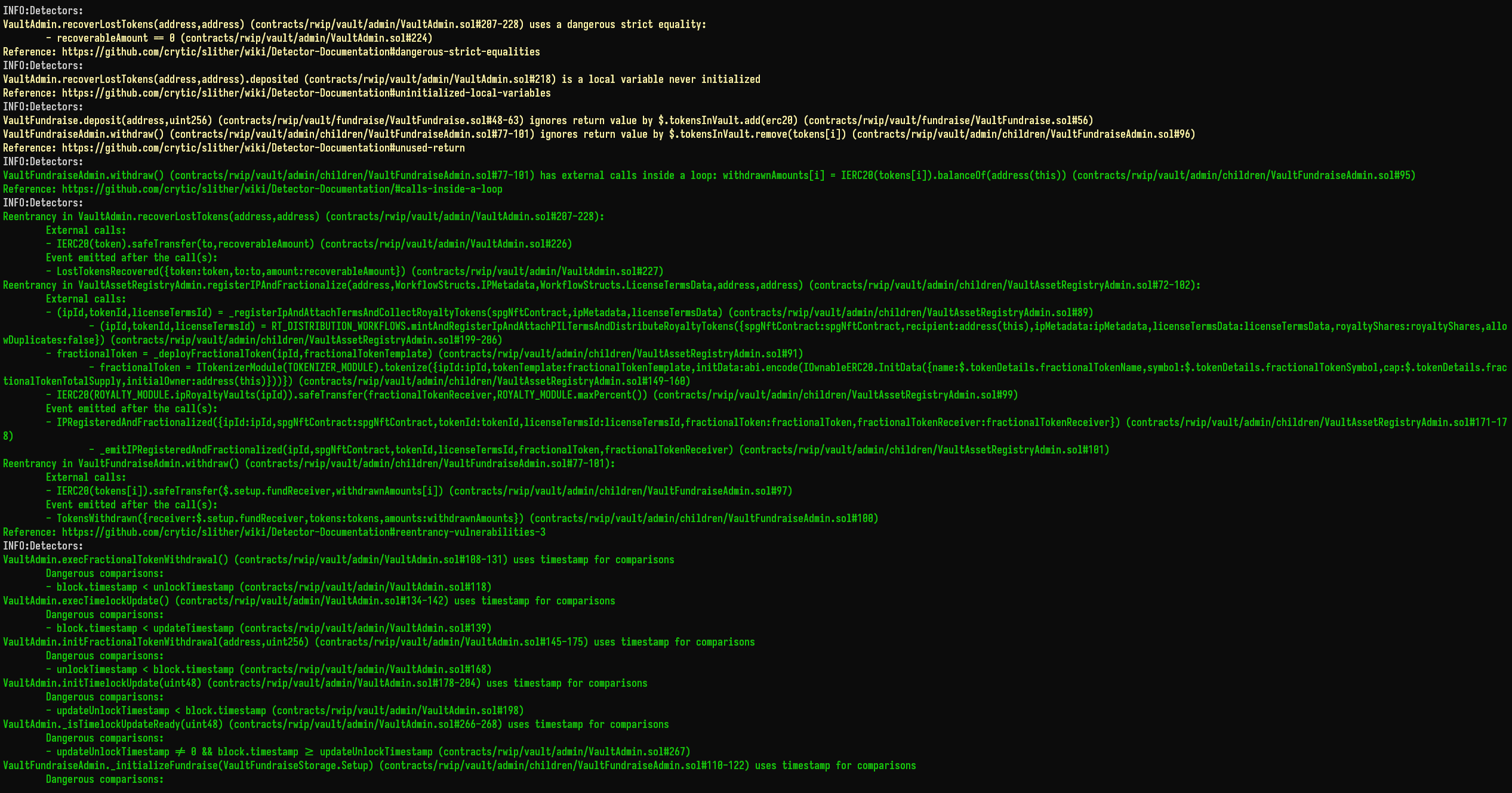
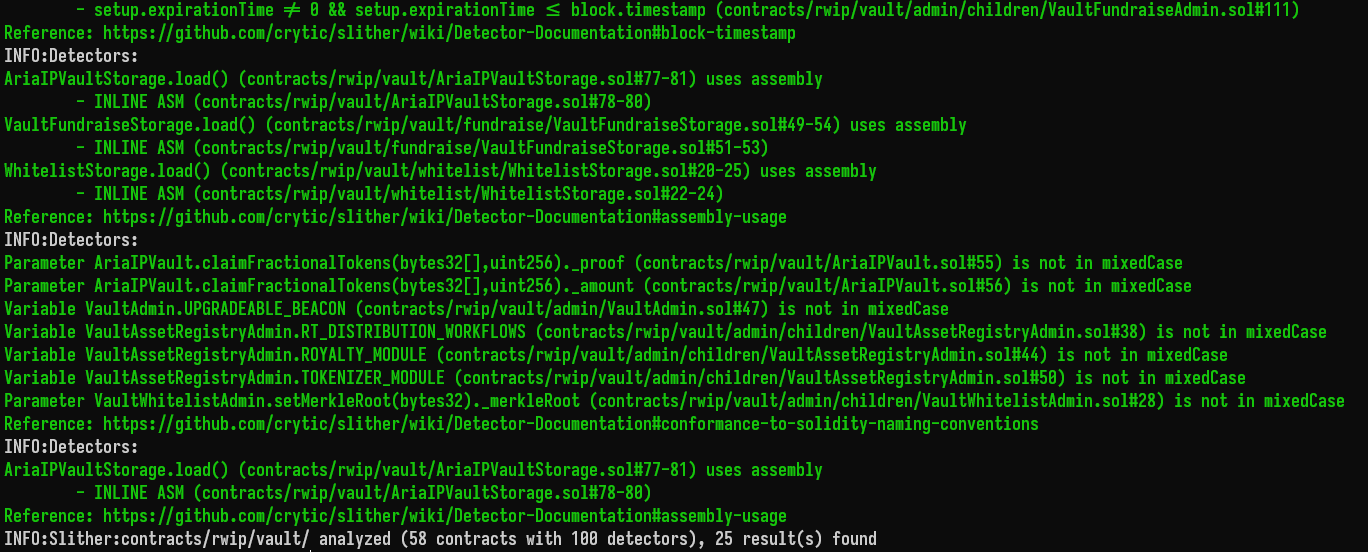
Halborn used automated testing techniques to enhance the coverage of certain areas of the smart contracts in scope. Among the tools used was Slither, a Solidity static analysis framework. After Halborn verified the smart contracts in the repository and was able to compile them correctly into their abis and binary format, Slither was run against the contracts. This tool can statically verify mathematical relationships between Solidity variables to detect invalid or inconsistent usage of the contracts' APIs across the entire code-base.
The security team assessed all findings identified by the Slither software, however, findings with related to external dependencies are not included in the below results for the sake of report readability.
The findings obtained as a result of the Slither scan were reviewed, and some were not included in the report because they were determined as false positives.
| EXPLOITABILITY METRIC () | METRIC VALUE | NUMERICAL VALUE |
|---|---|---|
| Attack Origin (AO) | Arbitrary (AO:A) Specific (AO:S) | 1 0.2 |
| Attack Cost (AC) | Low (AC:L) Medium (AC:M) High (AC:H) | 1 0.67 0.33 |
| Attack Complexity (AX) | Low (AX:L) Medium (AX:M) High (AX:H) | 1 0.67 0.33 |
| IMPACT METRIC () | METRIC VALUE | NUMERICAL VALUE |
|---|---|---|
| Confidentiality (C) | None (C:N) Low (C:L) Medium (C:M) High (C:H) Critical (C:C) | 0 0.25 0.5 0.75 1 |
| Integrity (I) | None (I:N) Low (I:L) Medium (I:M) High (I:H) Critical (I:C) | 0 0.25 0.5 0.75 1 |
| Availability (A) | None (A:N) Low (A:L) Medium (A:M) High (A:H) Critical (A:C) | 0 0.25 0.5 0.75 1 |
| Deposit (D) | None (D:N) Low (D:L) Medium (D:M) High (D:H) Critical (D:C) | 0 0.25 0.5 0.75 1 |
| Yield (Y) | None (Y:N) Low (Y:L) Medium (Y:M) High (Y:H) Critical (Y:C) | 0 0.25 0.5 0.75 1 |
| SEVERITY COEFFICIENT () | COEFFICIENT VALUE | NUMERICAL VALUE |
|---|---|---|
| Reversibility () | None (R:N) Partial (R:P) Full (R:F) | 1 0.5 0.25 |
| Scope () | Changed (S:C) Unchanged (S:U) | 1.25 1 |
| Severity | Score Value Range |
|---|---|
| Critical | 9 - 10 |
| High | 7 - 8.9 |
| Medium | 4.5 - 6.9 |
| Low | 2 - 4.4 |
| Informational | 0 - 1.9 |
Critical
0
High
0
Medium
0
Low
2
Informational
5
| Security analysis | Risk level | Remediation Date |
|---|---|---|
| Missing state validation in claimFractionalTokens() function | Low | Solved - 05/12/2025 |
| Missing USDC address validation in fundraise initialization | Low | Risk Accepted - 05/12/2025 |
| Lack of uniqueness validation for token identifiers across vaults | Informational | Acknowledged - 05/12/2025 |
| Contract size too big for deployment | Informational | Solved - 05/12/2025 |
| Suboptimal modifier ordering | Informational | Acknowledged - 05/12/2025 |
| Floating pragma | Informational | Solved - 05/12/2025 |
| Unused import | Informational | Solved - 05/12/2025 |
//Low
//Low
//Informational
//Informational
//Informational
//Informational
//Informational
Halborn strongly recommends conducting a follow-up assessment of the project either within six months or immediately following any material changes to the codebase, whichever comes first. This approach is crucial for maintaining the project’s integrity and addressing potential vulnerabilities introduced by code modifications.
// Download the full report
Vault Contracts
* Use Google Chrome for best results
** Check "Background Graphics" in the print settings if needed