Every distributed ledger makes a promise about shared truth. What most don’t say is that shared truth, taken literally, means shared data. And shared data is precisely what regulated financial institutions cannot afford.
At the most fundamental level, the problem is architectural. Public blockchains were designed around radical transparency, where every transaction, balance, and contract interaction sits on a ledger that anyone can read, trace, and analyze. For cryptocurrency transfers between pseudonymous wallets, that works well enough. For a derivatives desk managing billions in collateral positions or a custodian settling securities on behalf of institutional clients, that same transparency becomes an intelligence feed for competitors, a regulatory liability under data protection law, and an operational risk that no compliance team would approve. Despite the industry’s repeated assertions that distributed ledgers would replace the trust infrastructure of traditional finance, the transparency that makes public blockchains verifiable is the same property that has, until recently, made them unusable for the institutions they were supposed to serve.
Attempts to solve this by restricting visibility have historically introduced a different set of challenges. Private blockchains and permissioned networks preserve confidentiality by isolating participants into closed groups. In doing so, they often reintroduce reconciliation overhead, counterparty risk, and coordination failures that distributed ledgers were meant to eliminate. In many respects, institutions that adopted private chains to escape transparency found themselves managing similar reconciliation processes they had sought to leave behind, only now with distributed ledger infrastructure layered on top.
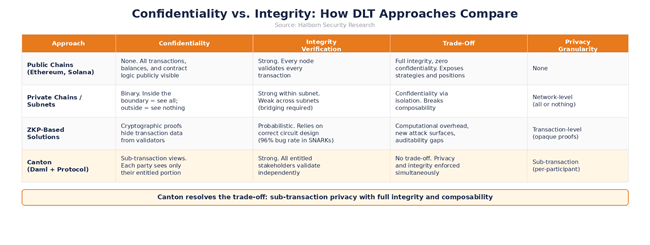
This has created a structural constraint that long defined institutional blockchain adoption. Existing platforms could generally provide integrity through shared visibility or preserve confidentiality through isolation, but not both at the granularity institutional finance requires. Though zero-knowledge proofs and other cryptographic approaches have attempted to solve this, the complexity they introduce, including a high rate of circuit-layer issues in documented SNARK vulnerabilities and implementation flaws such as the Zcash Sprout counterfeiting bug, has prevented them from delivering production-grade privacy for regulated finance. The result is an industry that has processed trillions in crypto-native volume, while regulated finance, the market that would benefit most from shared ledger infrastructure, has until recently remained largely on the sidelines.
Canton approaches this differently, enforcing need-to-know privacy at the sub-transaction level as a protocol property rather than an application-layer add-on. Hence, confidentiality and integrity coexist by construction rather than by compromise. As we explained in our previous article on threat modeling for Canton-based applications, Canton’s architecture creates distinct trust boundaries where each participant sees only what they are entitled to. This article examines how Canton resolves the confidentiality-integrity trade-off at the protocol level, why that resolution matters for regulatory compliance under GDPR and DORA, and which security risks remain even when privacy is enforced by design.
Why the Trade-Off Has Persisted
The tension between confidentiality and integrity in distributed ledgers is not a design flaw that better engineering will eventually fix but a structural consequence of how most protocols achieve consensus. Integrity on a distributed ledger means that all participants agree on the state of every contract and transaction. The most direct way to achieve this is full replication, which means giving everyone a copy of everything, letting everyone validate everything, and reaching consensus by majority agreement. Ethereum and most transparent public L1s operate this way. The approach is effective at producing a single, verifiable source of truth, but it achieves that truth by making everything visible to everyone.
Confidentiality requires the opposite by restricting who can see what. In traditional finance, this restriction comes from institutional boundaries. Your bank sees your account, but other banks don’t. Your custodian sees your holdings, and your counterparty’s custodian sees theirs. Privacy is a function of organizational separation, enforced by contracts, regulation, and physical infrastructure.
When you attempt to combine both properties on a single shared ledger, the contradiction becomes difficult to resolve. If everyone must validate, everyone must see. If everyone sees, nobody has confidentiality. And if you restrict visibility to preserve confidentiality, you lose the ability for all participants to independently verify the ledger’s integrity. Every platform that has tried to square this circle has ended up sacrificing one property for the other, or bolting on cryptographic complexity that introduces its own failure modes.
The regulatory dimension makes this trade-off even more consequential. The European Data Protection Board’s Guidelines 02/2025, adopted in April 2025, stated explicitly that blockchain technology is not exempt from GDPR requirements and that technical impossibility cannot justify non-compliance. For public blockchains where transaction data is immutable and globally visible, reconciling with data minimisation principles becomes an exercise in contradiction. The right to erasure remains architecturally challenging for any immutable ledger, including Canton, though sub-transaction privacy significantly reduces the scope of data that would require such treatment by limiting what is stored on each participant's ledger projection in the first place.
How Canton’s Sub-Transaction Privacy Model Works
Canton does not attempt to bolt privacy onto a transparent ledger. The protocol was designed from inception around a principle that mirrors how financial privacy actually works in practice. Its architecture ensures that participants see only what they are entitled to see and nothing more. The mechanism is sub-transaction-level privacy. When a transaction executes on Canton, it is not broadcast as a single atomic unit that every node receives and validates. Instead, the transaction is decomposed into views, where each view contains only the data relevant to a specific participant. A participant’s projection of a transaction is the minimal sub-transaction containing the actions on which that party is an informee.
Consider what this means for a concrete financial workflow. In a delivery-versus-payment (DvP) settlement where a buyer purchases 100 shares from a seller for $10,000, a conventional distributed ledger would require every validator to see both the cash movement and the securities transfer. In Canton, the bank handling the cash sees only the $10,000 transfer. The registrar handling the securities sees only the 100 shares moving. The buyer, seller, and trading application see both sides. Each participant validates their portion independently and the protocol ensures all validations converge on the same result.
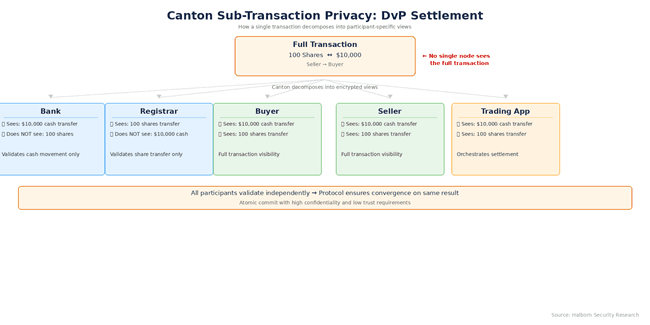
The sequencer, which orders transactions within a synchronization domain, does not learn the transaction contents. Communication between validator nodes is end-to-end encrypted, and data sharing follows strict need-to-know rules determined by the Daml contract’s authorization model through signatories, observers, and controllers.
The confirmation protocol reinforces this architecture. When a transaction is submitted, each entitled participant receives their encrypted view, validates it against the contract logic, and sends a verdict to the mediator. The mediator aggregates verdicts according to a confirmation tree, and once enough positive confirmations arrive from every authorizing party, it broadcasts the confirmation to all involved participants. The synchronizer learns the shape of the transaction through the confirmation tree structure, but not its contents. The result is an atomic commit that preserves both high confidentiality and strong integrity with minimal trust requirements.
What sets Canton apart is its composability. Validators can connect across multiple synchronization domains, forming a true “network of networks.” Cross-domain transactions execute atomically while each participant retains full control over what they disclose. In this way, Canton bridges the composability gap that earlier permissioned approaches could not fully close without reintroducing fragmentation or visibility trade-offs.
Broadridge’s Distributed Ledger Repo platform demonstrates what this architecture produces at an institutional scale. Built on Canton, DLR processed $5.9 trillion in repo transactions in August 2025, averaging $280 billion in daily volume. Each institution sees only its side of the transaction. In that same month, Bank of America, Circle, Citadel Securities, DTCC, Société Générale, and Tradeweb executed the first weekend on-chain funding transaction involving U.S. Treasuries and USDC on Canton, marking a step toward 24/7 capital markets that operate without the settlement gaps and overnight risk buffers that traditional infrastructure requires.
Security Implications of Need-to-Know Privacy
From a security standpoint, Canton’s privacy model eliminates several risk categories that continue to affect both transparent and bolt-on-privacy platforms.
On a public blockchain, a single compromised node exposes the full ledger. In Canton, the blast radius of any breach is bounded by the participant’s visibility scope since a compromised validator reveals only the data that the validator was entitled to hold. This is a meaningful difference when the alternative is a breach that exposes every transaction across every counterparty on the network.
On the other hand, transparent chains broadcast every transaction to every node, creating rich metadata that can be analyzed for trading patterns, counterparty relationships, and position sizes even without access to private keys. Canton’s selective distribution eliminates this attack surface. An observer outside a transaction’s stakeholder set learns nothing about it because the transaction does not appear on their ledger projection at all.
The front-running dynamics shift substantially on Canton. In transparent DeFi environments, pending transactions sit in public mempools where any sophisticated actor can extract value by front-running, sandwiching, or manipulating transaction ordering. Canton eliminates the public mempool as an attack surface, but the sequencer, which orders transactions within a synchronization domain, becomes a privileged observer of pending transaction flow. This relocates the extraction opportunity from an open field to a single operator, making sequencer governance, operational controls, and trust assumptions a first-order security concern. For regulated financial firms, the risk profile changes from broad-based MEV extraction by anonymous actors to a narrower trust dependency on sequencer operators, which is more manageable through contractual, governance, and monitoring controls but must be explicitly modeled rather than assumed away.
Moreover, Canton’s model also preserves auditability without sacrificing confidentiality. Because every action on the ledger is deterministically recorded from each participant’s perspective, audit trails remain complete for authorized parties. Regulators or auditors can be granted observer status on specific contracts, giving them visibility into the transactions they need to review without exposing the broader network’s activity. This selective disclosure satisfies GDPR’s data minimization requirements and DORA’s auditability mandates at the same time, a combination that ZKP-based approaches, with their opaque proofs, struggle to deliver.
What Sub-Transaction Privacy Does Not Solve
Canton's privacy model is strong, but treating it as a complete security solution would be a mistake. Several risk categories persist regardless of how well privacy is enforced at the protocol level.
Transaction timing patterns, volume spikes, and network activity levels can leak information to sufficiently motivated observers even when transaction contents remain invisible. An institution that consistently transacts at specific times or in response to market events may reveal behavioral patterns through timing alone. Metadata minimization, including batching and careful scheduling of operations, requires deliberate design work that the protocol does not enforce automatically.
A compromised validator node still exposes whatever data that validator was entitled to hold. While the damage is bounded compared to a public chain breach, the exposed data may still include sensitive contract states, counterparty identities, and transaction histories for hosted parties. Often, infrastructure hardening, HSM-backed key management, and real-time anomaly detection at the validator level remain non-negotiable.
Canton's privacy enforcement follows the authorization rules defined in Daml contracts with absolute fidelity. If a contract template grants observer rights to parties who should not have them, the protocol will faithfully enforce that overly broad visibility. Privacy is only as good as the contract model beneath it, making template auditing and careful authorization design a first-order security concern rather than something to address after deployment.
The moment data crosses from the ledger into external systems, whether APIs, data feeds, reporting tools, or analytics platforms, Canton's privacy guarantees no longer apply. Integration boundaries between on-ledger and off-ledger infrastructure represent the highest-risk surfaces for data leakage and demand a zero-trust architecture, authenticated channels, and continuous monitoring.
Namespace keys, topology transactions, party-to-validator mappings, and certificate authorities all sit outside the privacy model's scope but control who can participate and under what authority. Compromise at the governance layer can undermine the privacy guarantees above, making structured key management and governance security operationally critical for any Canton deployment.
Beyond protocol-level concerns, Canton-specific contract attack classes deserve explicit modeling. Contention attacks exploit Canton's optimistic concurrency by racing exercises on hot contracts to deny service to legitimate users. Divulgence chains leak contract state to intermediate actors through nested exercises, distinct from observer misconfiguration. Fetch-by-key operations leak the existence (or absence) of contracts to the fetching party. Sub-transaction correlation attacks allow an adversary controlling multiple participants to reconstruct information no single ledger projection should reveal. These attack classes are unique to Canton's privacy model (they exist on neither public chains nor permissioned alternatives) and require Canton-specific audit expertise to detect during template review.
These governance considerations are themselves evolving. As of early 2026, the Canton Network operates as a production-grade open network powered by its native Canton Coin and a growing set of Super Validators, including major institutions such as DTCC, Circle, Chainlink Labs, and others operating with defined governance weights. These Super Validators play a critical role not only in consensus and ordering but also in shaping network evolution through weighted governance. Incentive mechanisms, including per-round rewards and provisions that encourage long-term alignment, aim to support network health. This shift from purely permissioned origins toward a more decentralized yet institutionally anchored model alters trust assumptions. This means that while sub-transaction privacy remains enforced at the protocol level, participants must now account for the economic and governance incentives influencing Super Validator uptime, upgrade coordination, and potential collusion vectors at the metadata layer. The design continues to bound blast radius through need-to-know rules, but institutions deploying at scale should incorporate these evolving incentives into their threat models and operational due diligence.
This fidelity to the contract model cuts both ways. Unlike Solidity-based environments, Daml's functional design and explicit signatory/observer model eliminate entire classes of vulnerabilities at compile time (most notably reentrancy). Yet new risk categories emerge that institutions must treat as first-order concerns. Conservation violations remain a persistent threat in multi-leg workflows, especially when assets move across several transfer paths. The invariant that total inputs must equal total outputs can break subtly if every execution path is not exhaustively verified. Observer-rights misconfigurations compound the issue, as a contract template that inadvertently grants broad visibility to parties that should remain outside the need-to-know boundary will see that exposure enforced by the protocol itself. Cross-domain settlement edge cases introduce further complexity, where ledger-time assumptions or non-deterministic ordering across synchronizers can lead to rejected transactions or, worse, inconsistent finality under production load. In short, the protocol is only as secure as the contract model beneath it. Template auditing, formal verification of conservation properties, and rigorous testing of authorization logic are structural requirements for any deployment handling material notional value.
Canton vs. ZK-Based Privacy Chains – A Security Practitioner’s View
Canton approaches privacy differently from platforms that attempt to retrofit confidentiality onto otherwise transparent ledgers. Rather than layering zero-knowledge proofs atop a system designed for full replication, Canton embeds need-to-know visibility directly into the protocol and the Daml contract model. This structural approach delivers meaningful advantages for institutional operators. Privacy guarantees become auditable by construction, enabling an authorized party to inspect exactly what the protocol revealed and why, without having to trust opaque proof generation or verification circuits. In contrast, ZKP-based solutions, while cryptographically elegant in theory, continue to carry fragility at the circuit and implementation layer, particularly where under-constrained arithmetic, soundness bugs, and subtle prover-verifier mismatches have repeatedly surfaced in production systems. For regulated financial institutions that must demonstrate compliance to auditors and regulators, Canton’s model offers clearer evidentiary trails and simpler assurance arguments. The trade-off is deliberate since Canton relies on well-governed participants and hardened infrastructure rather than pure cryptographic opacity. Both paths have merit, but for workflows demanding programmable, composable privacy at scale today, the structural enforcement of Canton has proven more immediately operable and auditable in live institutional environments.
To illustrate these architectural distinctions more clearly, the following comparison highlights how Canton differs from both fully transparent public chains, cryptographic bolt-ons, and earlier permissioned approaches.
Dimension | Public Blockchains | ZK-Based Privacy Chains | Permissioned Chains | Canton Network |
Privacy Model | Full transparency; all participants see entire state | Cryptographic opacity layered on transparent ledger | Isolation via closed groups; no shared visibility | Sub-transaction need-to-know privacy by protocol construction |
Integrity & Validation | Global replication; every node validates everything | Relies on proof verification; soundness depends on circuit integrity | Local validation within silos; reconciliation required | Entitled participants validate only their view; atomic convergence via mediator |
Composability | High within visible state; cross-chain requires bridges | Limited by proof complexity and shared visibility | Low; fragmentation reintroduces bilateral processes | High across synchronization domains without sacrificing privacy |
Front-Running / MEV Risk | High (public mempools expose pending transactions) | Reduced but not eliminated (metadata and ordering visible) | Low (isolated networks) | Public mempool MEV eliminated; ordering authority relocates to sequencer operator (narrower, governable trust dependency) |
Auditability | Difficult selective disclosure; conflicts with data minimization | Opaque proofs complicate evidentiary trails | Selective but lacks shared truth | Built-in observer roles enable precise, compliant visibility |
Residual Risks | Full ledger exposure on node compromise; metadata analysis | Circuit bugs, implementation flaws, prover trust | Reconciliation overhead and counterparty risk | Bounded by visibility scope; contract model fidelity, metadata timing, governance |
Institutional Readiness | Strong for crypto-native; regulatory friction for finance | Promising but audit-heavy due to cryptographic fragility | Familiar but fails at network effects | Production-proven at scale (e.g., Broadridge DLR) with structural privacy |
Recommendations for Secure Canton Deployments
Every Canton deployment intended for regulated financial activity should undergo disciplined security validation tailored to its architecture. Specifically:
(a) formal verification or exhaustive model-based testing of Daml contract templates (Daml-native formal verification tooling is evolving, so deployments should combine emerging native tools with TLA+ or Alloy modeling for critical state machines) with particular focus on conservation invariants, authorization logic, and cross-domain edge cases;
(b) penetration testing and hardening review of validator infrastructure, including HSM-backed key management and anomaly detection; and
(c) zero-trust audit of all integration boundaries where ledger data flows into external systems, APIs, or reporting platforms.
These steps, executed by teams experienced with Canton’s unique trust boundaries, represent the practical difference between theoretical privacy and production-grade resilience.
Canton in Regulated Finance
Financial privacy, especially at institutions that evaluate infrastructure decisions against fiduciary obligations, regulatory exposure, and competitive risk alongside performance and scalability, is a prerequisite for participation in any shared infrastructure. Regulations, including GDPR, the Gramm-Leach-Bliley Act, MiFID II’s pre-trade transparency exemptions, and Basel III’s capital adequacy requirements, all assume that institutions control who sees their positions, strategies, and client information. Any distributed ledger that cannot guarantee this control is, by default, non-compliant for most institutional use cases.
Canton’s sub-transaction privacy model resolves the confidentiality-integrity trade-off that has long constrained regulated finance’s adoption of shared ledger technology. Integrity is maintained because all entitled stakeholders independently validate their portion of every transaction. It preserves confidentiality as no participant sees more than what the contract’s authorization rules grant them. And composability, long a challenge for earlier permissioned approaches, remains intact because validators connect across synchronization domains without sacrificing privacy or integrity. For the first time, a distributed ledger platform delivers all three properties simultaneously at institutional scale. This is why Broadridge’s DLR processed $5.9 trillion in repo volume in August 2025 and why a growing roster of institutions, including Goldman Sachs, BNY Mellon, Broadridge, and the DTCC, are actively building on Canton.
The remaining work, such as contract design discipline, integration boundary security, key management governance, and continuous threat modelling, is important. These are precisely the areas where specialized security expertise proves most valuable. The forthcoming Zenith EVM execution layer expands Canton's application surface and introduces new cross-VM security considerations, which we address separately.
Building privacy-preserving financial infrastructure on Canton requires security practices tailored to its unique architecture. At Halborn, we provide blockchain security audits, penetration testing, and security consulting for Daml and Canton implementations. Whether you are designing contract authorization models, auditing validator infrastructure, or securing cross-domain workflows, our team can help ensure your privacy guarantees hold under adversarial conditions. Contact us to discuss your distributed ledger security needs.
